Pawel Rzepa
@rzepsky
Yet another sec guy, particularly interested in cloud security 🌩️ AWS Authorized Instructor at @awscloud
Lead Ethical Hacker at @SoftServeInc
ID: 3320585656
12-06-2015 08:30:43
1,1K Tweet
1,1K Takipçi
686 Takip Edilen



A good example of threat lists in CI/CD: storage.googleapis.com/prd-engineerin… This 👆 is part of the worth-reading article: engineering.mercari.com/en/blog/entry/… by Mercari Developers


This was cool to read :) Thanks Pawel Rzepa ! rzepsky.medium.com/aws-and-hacker…






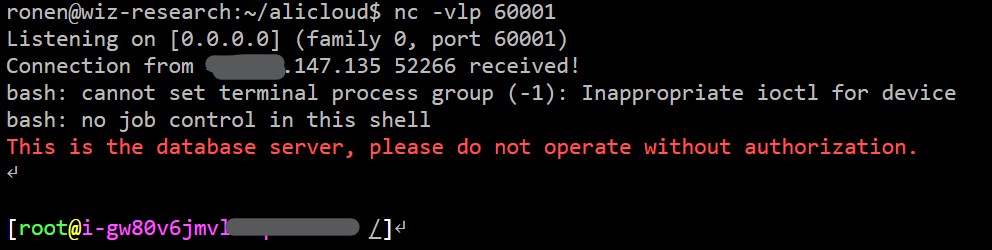
I hacked into a @Bing CMS that allowed me to alter search results and take over millions of Office 365 accounts. How did I do it? Well, it all started with a simple click in Microsoft Azure… 👀 This is the story of #BingBang 🧵⬇️







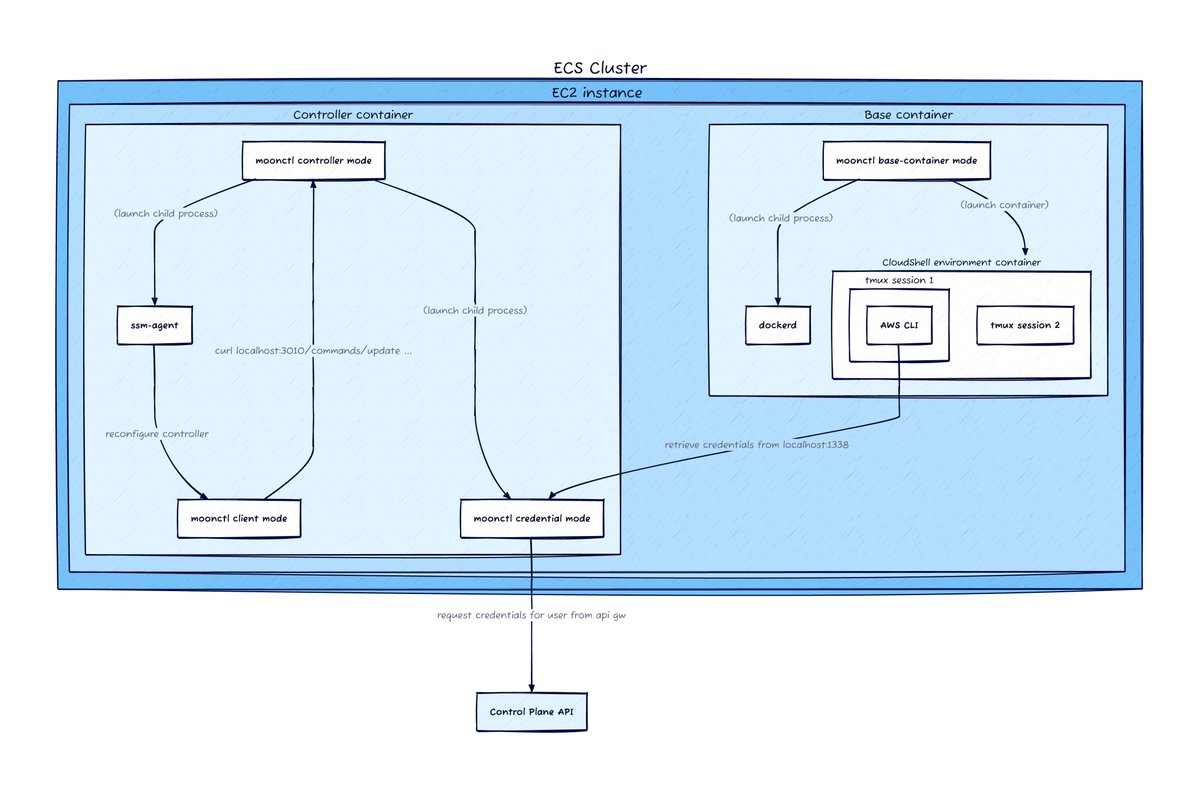
Thank you everyone who attended my talk fwd:cloudsec! The slides are here: frichetten.com/fwdcloudsec-20…