MoBustami
@mobustami
Malware Researcher, Internet Protector, Cyber researcher
ID: 1640752537
02-08-2013 15:37:36
2,2K Tweet
476 Takipçi
297 Takip Edilen

Anybody got a good place/website for Ugly Christmas sweater APT style? Think of crowdstrike APT logos but on a Christmas sweater, any idea Tyler McLellan chicagocyber J. A. Guerrero-Saade Katie Nickels





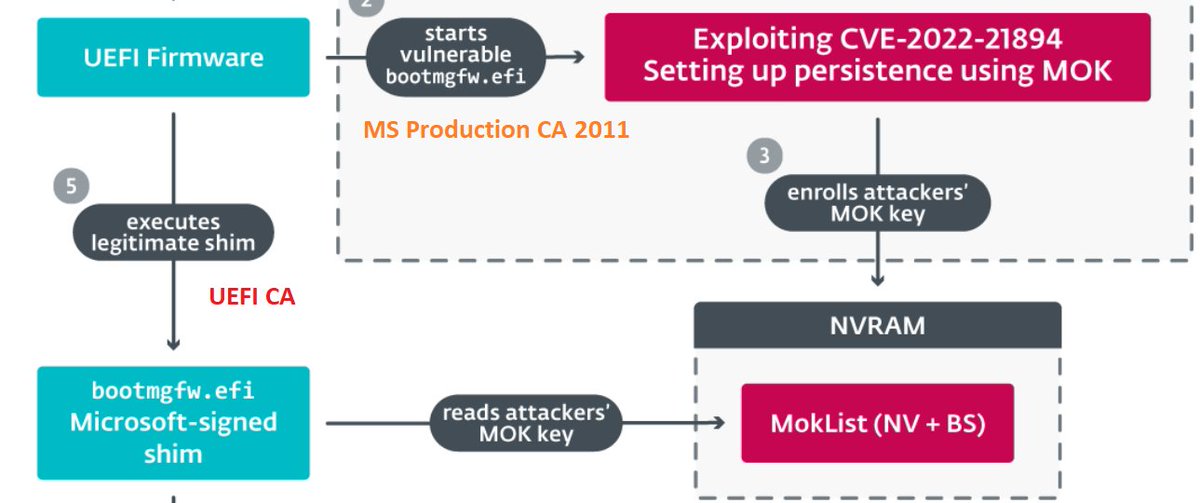
My 2c on the #BlackLotus UEFI bootkit (thanks, ESET Research): - "Exploitation Less Likely" is proven wrong, hope for a new DBX revocation list. - not trusting UEFI CA saves the day yet again. - having a single NV+BS variable as a gateway to booting whatever is a bad idea.


Thank you Andrew Thompson for this... I could not have said it any better