Adebayo_Abdulmalik_Olanrewaju
@malik_cybersec
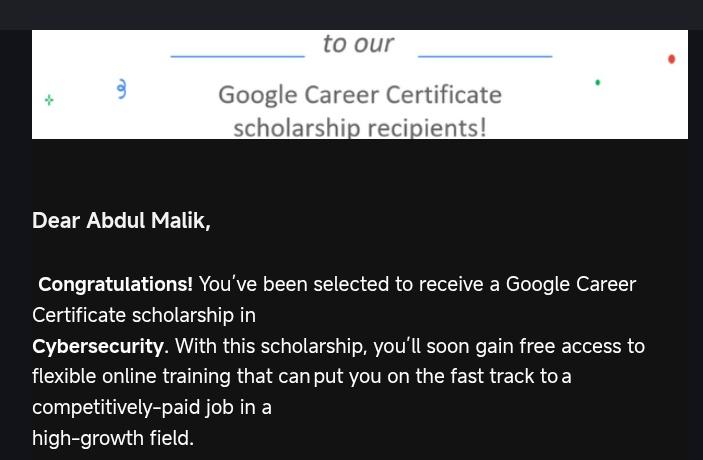
Cyber_Security_Student ( Aspiring_pentester)||BSc Cybersecurity ⏳|| ISC² CC ⏳|| Junior Cybersecurity Analyst ⏳|| Front_end_Web_Dev
ID: 1704022448880979968
19-09-2023 06:43:30
48 Tweet
50 Takipçi
76 Takip Edilen


I attended Cyber fair 2.0 last week , hosted by NACSS under the lead of Tory☁️ as the departmental president, it was a great experience meeting with some of my mutual Mr. Henry The Lightsome Delightsome 🤓☁️ and some of the panelists Olúmáyòwá.dev cybernerd🤖 Looking forward to 3.0




Josh Abdulmalik_cybersecurity Nana Sei Anyemedu Magnet RAM Capture because i see it to be a lightweight imaging tool from Magnet Forensics designed to capture physical RAM on both Windows and Mac. It has a small footprint, minimizing the alteration of the memory being captured.



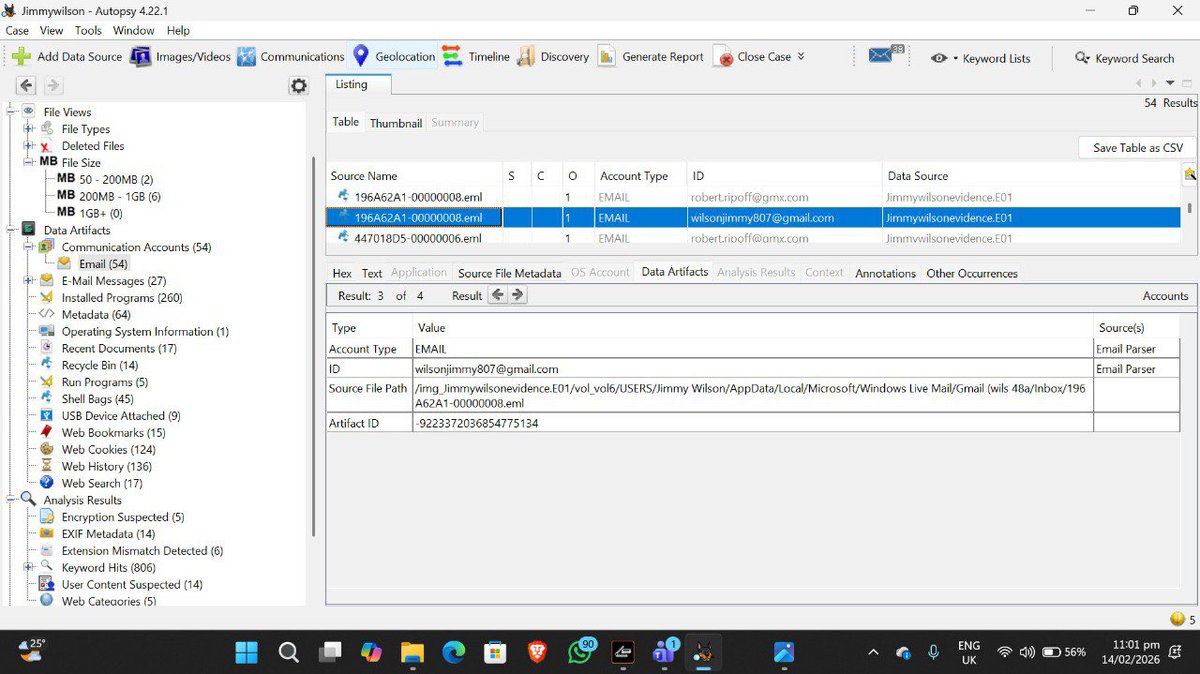
Today I practiced Email Forensics to trace a message back to its source. By digging into the headers, I extracted the source IP , geolocated it, and verified the SPF/DKIM/DMARC authentication. Verified evidence is the only evidence🕵️♂️🛡️ Nana Sei Anyemedu 💚 #CyberSecurity







Just completed Networking Academy CCNA 1-3 and earned a discounted exam voucher! 🚀 Grateful to Olúmáyòwá.dev, TechPeak Lab, & Lancelot eihoda for the opportunity. Invaluable gains in network infra, IP addressing, & security. Next stop: Certification! 💪 #CCNA


Grateful to have completed the 3-stage program by Tech Peak Lab! TechPeak Lab As a reward, I received a 58% voucher discount for the CCNA exam 🎉 Thank you for investing in learners and making professional certifications more accessible. On to the next milestone! #CCNA



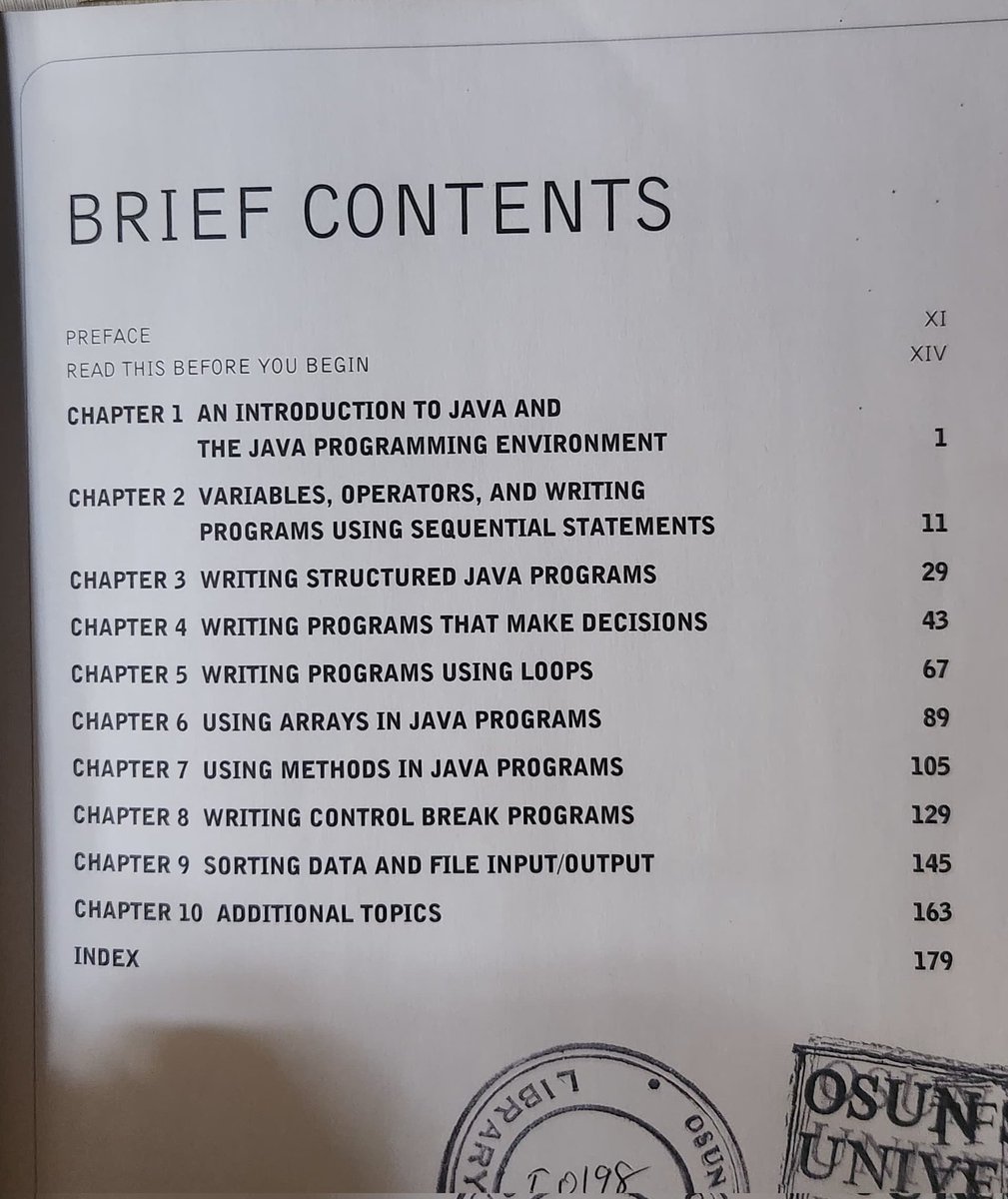
Over the last two weeks I have been learning Java Why Java? I have had it in mind to learn it and I got to know I will be doing Java two weeks to exam . Went to the school library and get myself some books. Stay tuned while I build something after exam Elorm Daniel Dr Iretioluwa Akerele