
Asger.jpg
@hackerkartellet
🇩🇰 living in 🇩🇪
Principal IR dude trying to do IR stuff at @InfoGuardAG
infosec.exchange/@hackerkartell…
@hackerkartellet.bsky.social
ID: 235381041
08-01-2011 01:41:35
204 Tweet
638 Takipçi
965 Takip Edilen







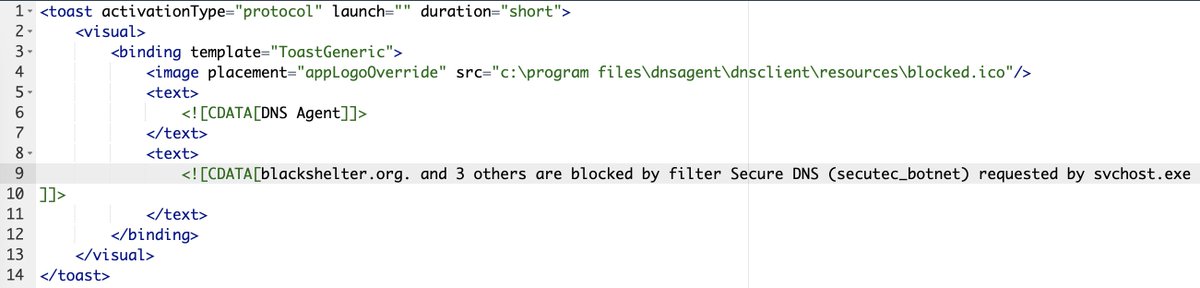
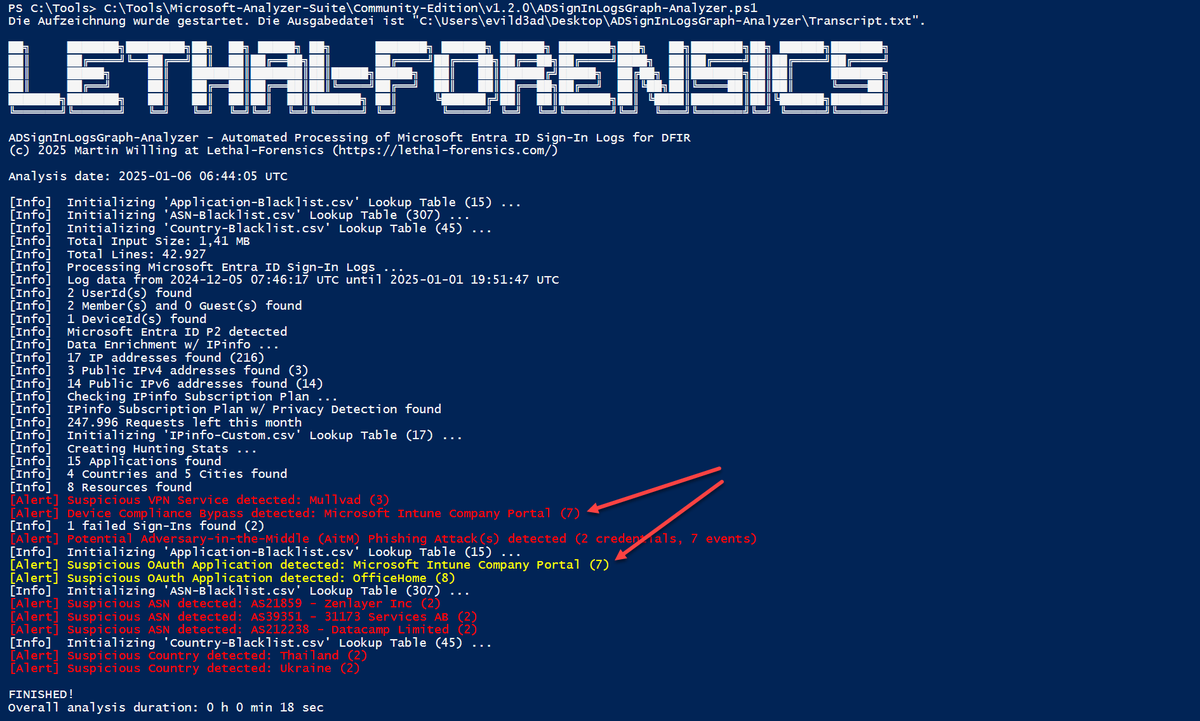
I just released Microsoft-Analyzer-Suite v1.3.0. UserAgent Blacklist added, ClientInfoString and Mailbox Synchronization detection of eM Client (Traitorware) added, and much more. Happy M365 Threat Hunting! Invictus Incident Response #M365 #Entra #BEC #DFIR github.com/evild3ad/Micro…














![Stephan Berger (@malmoeb) on Twitter photo Yesterday, I presented "Anti-Forensic" techniques for Windows and Linux at the Troopers conference in Heidelberg. This morning at breakfast, I was approached by an attendee and asked if I had looked at the zapper tool from The Hacker's Choice. [1]
I said no, but of course, my Yesterday, I presented "Anti-Forensic" techniques for Windows and Linux at the Troopers conference in Heidelberg. This morning at breakfast, I was approached by an attendee and asked if I had looked at the zapper tool from The Hacker's Choice. [1]
I said no, but of course, my](https://pbs.twimg.com/media/GuXDZZEWsAA8lQY.png)