Gohanckz
@gohanckz
Exploit the world :)
ID: 754864549958856704
18-07-2016 02:25:08
256 Tweet
245 Takipçi
454 Takip Edilen










GitLab Authentication Bypass (CVE-2024-45409) : blog.projectdiscovery.io/ruby-saml-gitl… credits Harsh Jaiswal Rahul Maini




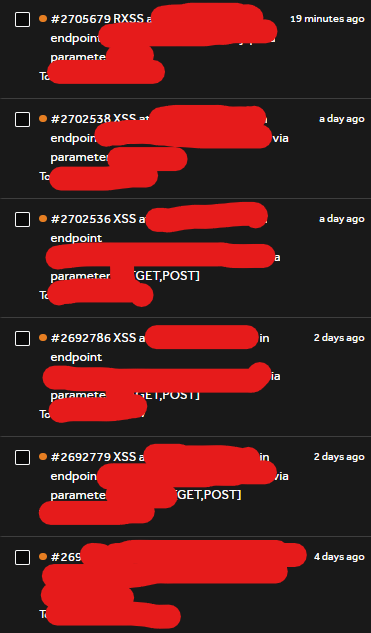
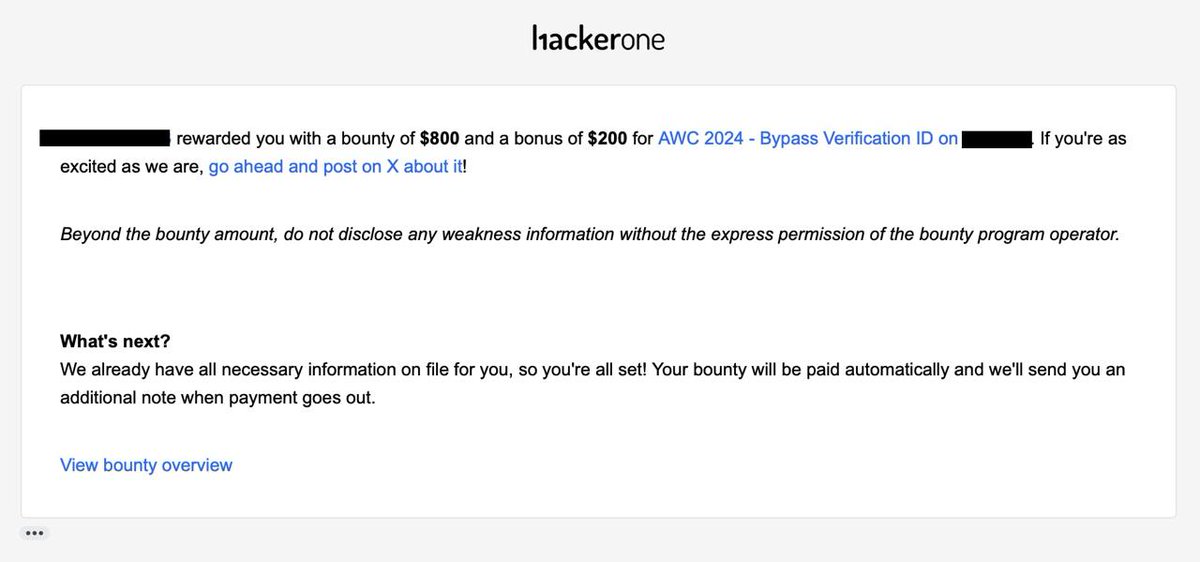
A mini-thread on how I approached this "Stored XSS with CSP Bypass" together with 2sharthegreat and popped it on our second day of hunting on that target (1/x): 👇 #bugbounty