Cyber security entrepreneur, chairman @csirt_global, volunteer @divdnl, formerly @foxit, @orangecyberdef, @cybersprintnl, and @ogd_ict
ID: 98913502
http://www.3esec.com 23-12-2009 16:30:58
3,3K Tweet
949 Takipçi
520 Takip Edilen

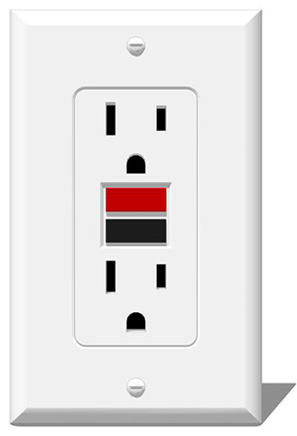
I can't stop thinking about an analogy Aanchal Gupta (Aanchal Gupta) made in her #BlueHat 2023 keynote. Consider the humble, everyday GFCI outlet:


New: we proved it could be done. I used an AI replica of my voice to break into my bank account. The AI tricked the bank into thinking it was talking to me. Could access my balances, transactions, etc. Shatters the idea that voice biometrics are foolproof vice.com/en/article/dy7…



We're prepping for FIC in Lille, from April 5 through 7. Co-founders Victor Gevers and [email protected] will be there, and Victor will keynote about global challenges in chasing vulnerabilities.







Ook ik sta op de lijst van duizenden crediteuren van #mtgox... Zo ben ik met Eline in contact gekomen. Deze aflevering speel ik ook een rolletje; en ontrafelt Eline Ronner de cybercrime-FSB-witwas spaghetti van 10 jaar geleden verder.





📣 Yesterday, we proudly announced the “Cyber Secure The Hague: NGO Support Program” at #ONE2023 together with a non-profit consortium consisting of us @CyberPeaceInst, The Hague Humanity Hub, Dutch Institute for Vulnerability Disclosure & @CSIRT_global, co-funded by City of The Hague Get to know the project in this thread ⬇️

A free Introduction to Cybersecurity course with me as your instructor is available on SkillsforAll. Thousands of students are already enrolled. The course begins on Oct 23, 2023. Let's make the internet a safer place, one student at a time. DIVD Academy divd.academy/courses/introd…