Adewale Mustapha
@adesecure
Cyber Security Engineer
ID: 2450618077
18-04-2014 00:41:20
602 Tweet
306 Takipçi
3,3K Takip Edilen



🌟 #Snowman (SNOW), the official meme coin of Ice Open Network, released as a fair launch on #Uniswap Trade Now: dexscreener.com/ethereum/0xd1f… 🙌 Join me on #Ice "walexzzy"


Just applied for the $Avive Airdrop! 🚀 Excited to join the #Avive community and be part of this journey. Don’t miss out – check out Avive World and see what they have in store! #AviveCitizens #AviveTestnet #AviveApp avive.world/avive_withdraw…



Give Away Alert!! 1. Artificial Intelligence 2. Machine Learning 3. Cloud Computing 4. Ethical Hacking 5. Data Analytics 6. AWS Certified 7. Data Science 8. BIG DATA 9. Python 10 MBA For 24 Hours only!! To get it: 1. Follow Parul Gautam (so I can DM) 2. Like &

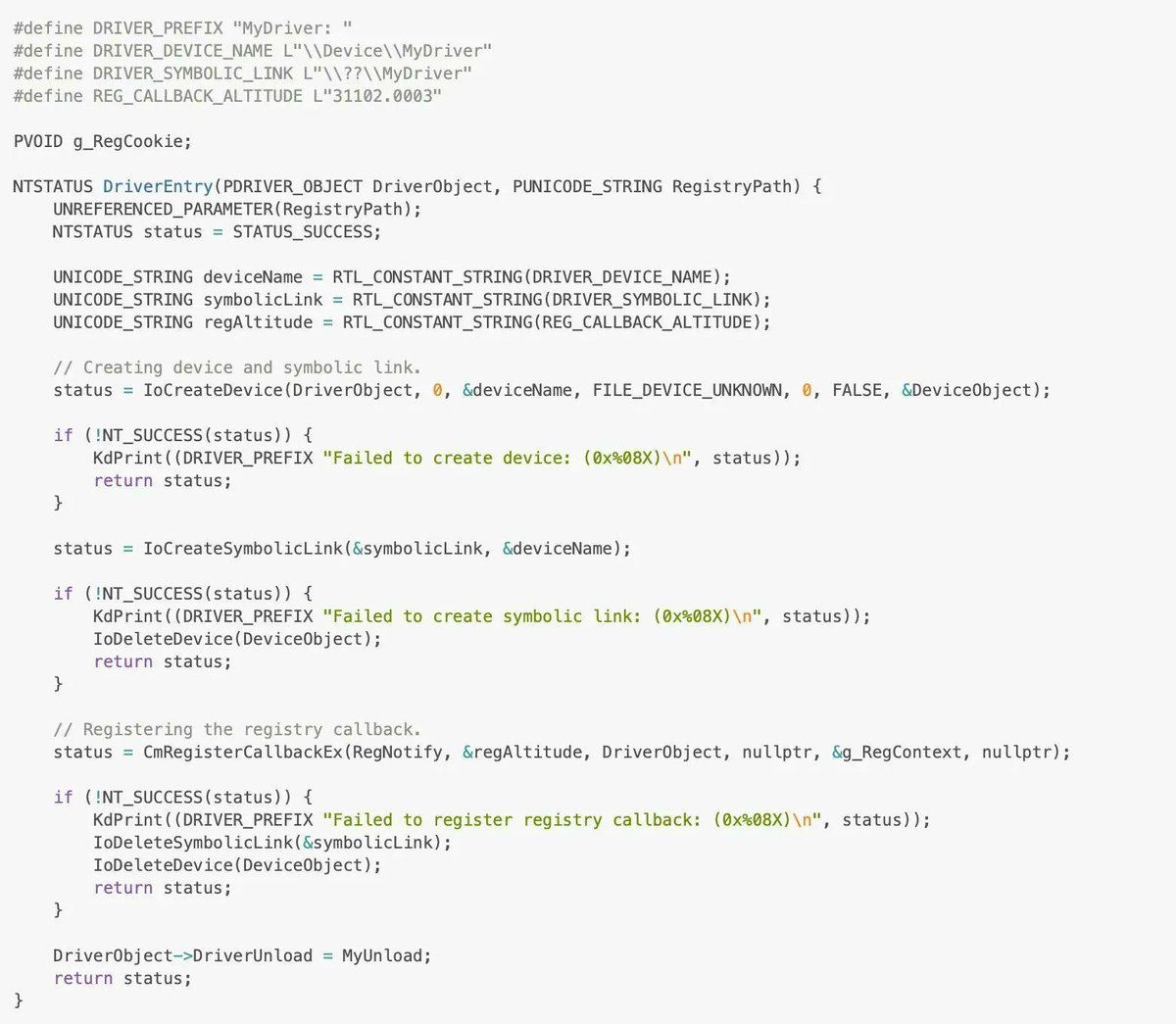
Windows rootkit development for red teaming and adversary emulation by Ido Veltzman Part 1: idov31.github.io/2022/07/14/lor… Part 2: idov31.github.io/2022/08/04/lor… Part 3: idov31.github.io/2022/10/30/lor… Part 4: idov31.github.io/2023/02/24/lor… PArt 5: idov31.github.io/2023/07/19/lor… #windows #cybersecurity

📚The #ProtonPrivacyReadingList is back! If you’re not a #cybersecurity professional, but you're looking to dive deeper into the subject, our friend C:\hristina has you covered. (1/2)





Dr Oludayo Sokunbi Dr Iretioluwa Akerele SherryRahman 🇳🇬 🇨🇦 Ozioma Chucks Think of it this way; A phishing mail sent to the victim to capture the victim credential or just sniff all his activities with a network sniffing tool. (Fiddle or Wireshark) Attack is possible if the device was on the same network while the person went to bed.