Michael Kruger
@_cablethief
Security analyst.
Random code bits at github.com/Cablethief/
ID: 202029919
13-10-2010 04:18:22
92 Tweet
629 Takipçi
361 Takip Edilen

Thats a wrap for the Hack The Box Business CTF 21. We played as the Orange Cyberdefense / Orange Cyberdefense's SensePost Team team and placed 5th! I'm super proud of the team, and all the hard pwntime they put it! Get some zzz's Inactive Account Jacques Coertze szymon Titanex @ defcon Michael Kruger @gav1no_ @gmilte!




🎉We're super excited to publicly release assless-chaps, our super fast MSCHAPv2 cracking tool github.com/sensepost/assl… Our DEF CON RF Hackers Sanctuary Village talk with Michael Kruger & me explaining it is out youtube.com/watch?v=lm7Cuk… Our new hashcat modes 27000/27100 have been merged too!

.Michael Kruger found the perfect shirt on Amazon for our talk. So I bought it for him, sort of. amazon.com/Ask-About-Assl…



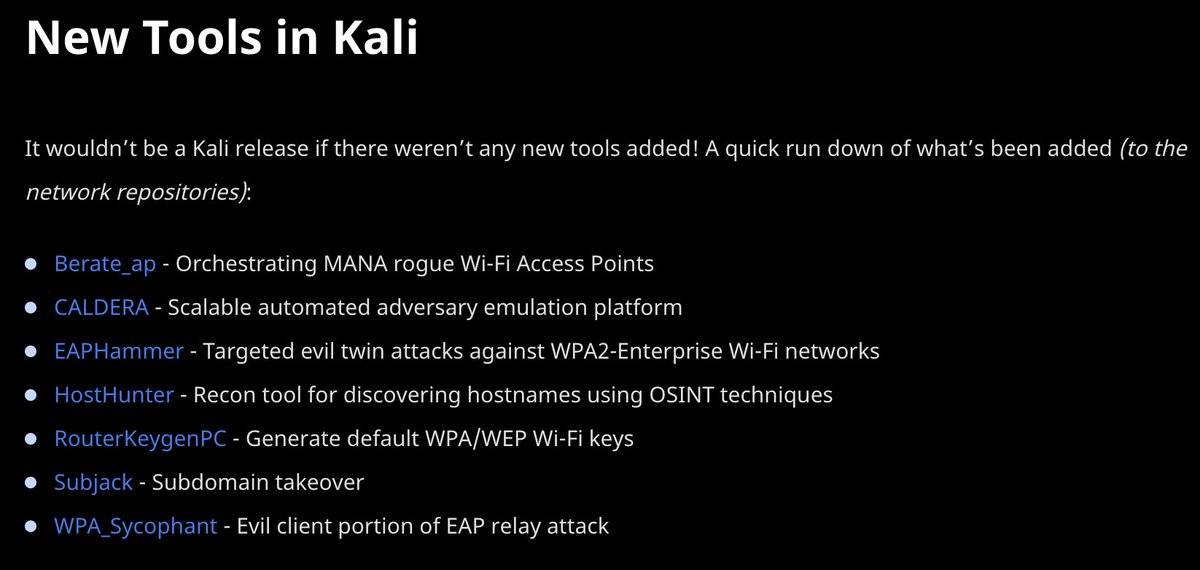
Good luck to all the trainers at @athackcon in #SaudiArabia! To the Orange Cyberdefense's SensePost Team crew - may it be a great kickstart to getting back to in person training. Smash it! #atHackcon #BlackHat #orangecyberdefense

The crew! @athackcon has been amazing. Saudi has been amazing. Training's pretty darn good. Conference has a great line up. Jason is one happy dude. Thanks SensePost Training | Orange Cyberdefense Orange Cyberdefense Orange Cyberdefense's SensePost Team @athackcon الاتحاد السعودي للأمن السيبراني والبرمجة والدرونز




Struggling to proxy your offensive tools (*cough, Windows, cough*)? See how Michael Kruger uses WireGuard and tun2socks to make remote networks available via a network route (from any device or container), over SOCKS! sensepost.com/blog/2022/wire…

Another 0xC0FFEE session tonight with two guest speakers: Jeandre Mitton talking about using Pre/Post Scripts with Postman for CAPTCHA bypass and _leon_jacobs(💥) talking about the LightNeuron malicious mail transport agent he built for MITRE ATT&CK purple teaming. 1/2

The RID500 Admin account doesn't benefit from Protected User Group restrictions. This is a MS WONTFIX & means you can authenticate as Admin using RC4 KRB or perform any KRB delegation attack if you impersonate the RID500 Admin. The latest find by Aurélien Chalot sensepost.com/blog/2023/prot…


A quick Docker hostapd-mana RADIUS service for capturing creds using an external device: github.com/sensepost/bera… Bonus: Certificates with Lego and CF DNS are so convenient go-acme.github.io/lego/usage/cli… Bonus Bonus: join us at BH for further WiFi shenanigans blackhat.com/us-23/training…



Had a blast climbing Norwegian 🇳🇴mountains with some amazing people, Ole André V. Ravnås and Michael Kruger !


The fact that Andres Freund (Tech) didn't just write the whole xz thing off as "It's probably DNS" is honestly amazing.