Ryan Benson
@_ryanbenson
I do digital forensics and work on open source DFIR tools @Google. I kinda like web browsers, too. Not on Twitter often anymore, reach me at ryan 'at' dfir.blog
ID: 30110948
https://dfir.blog 10-04-2009 00:40:53
1,1K Tweet
4,4K Followers
267 Following




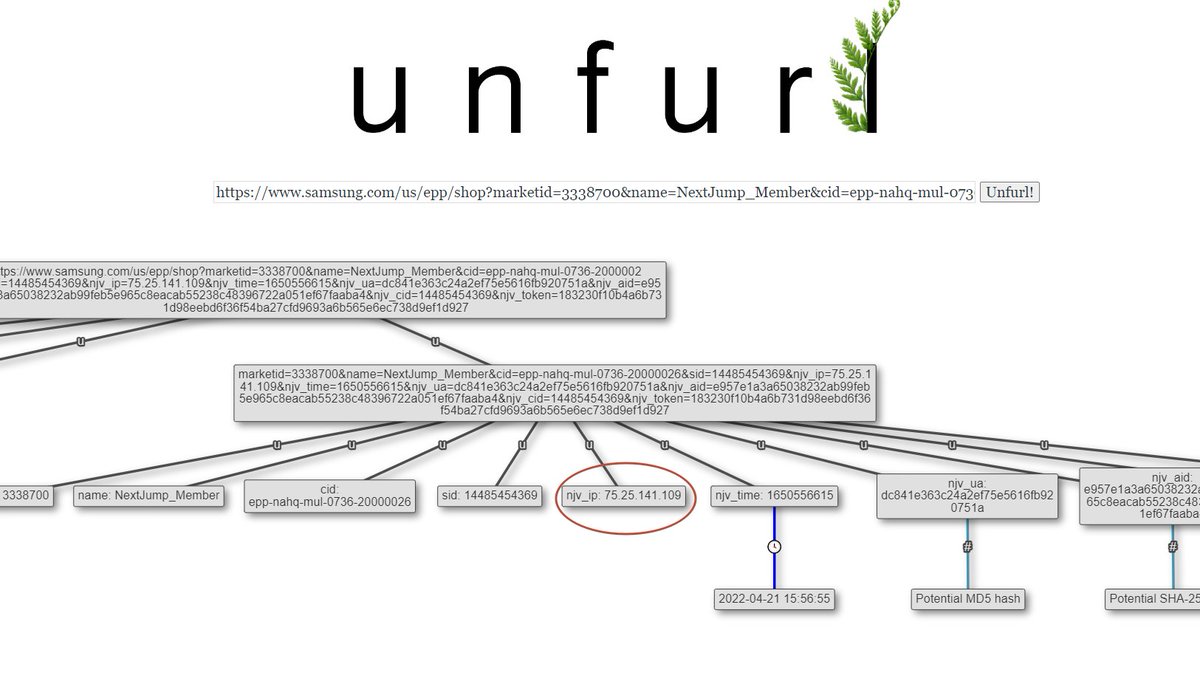
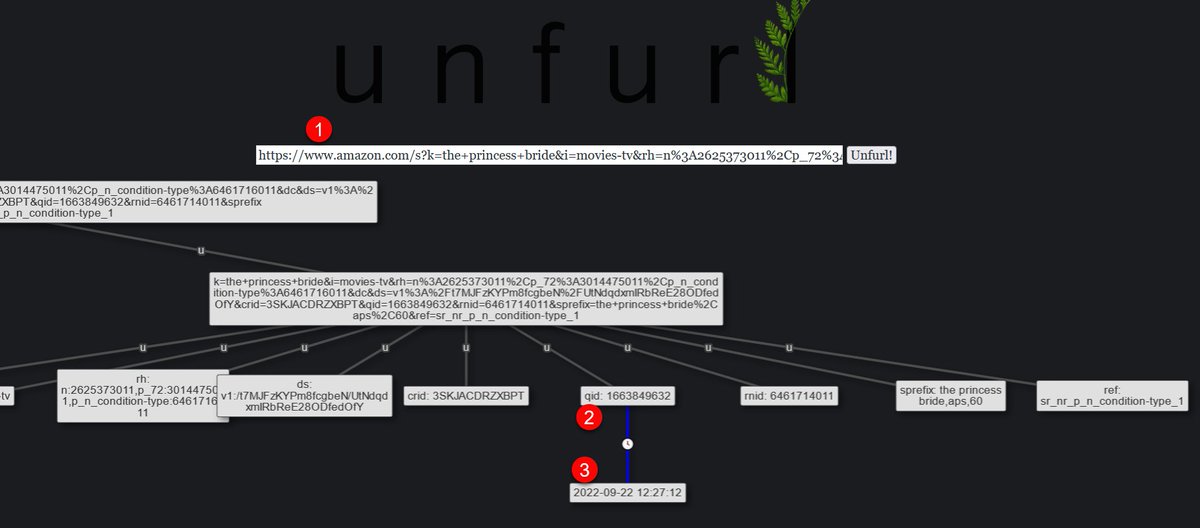
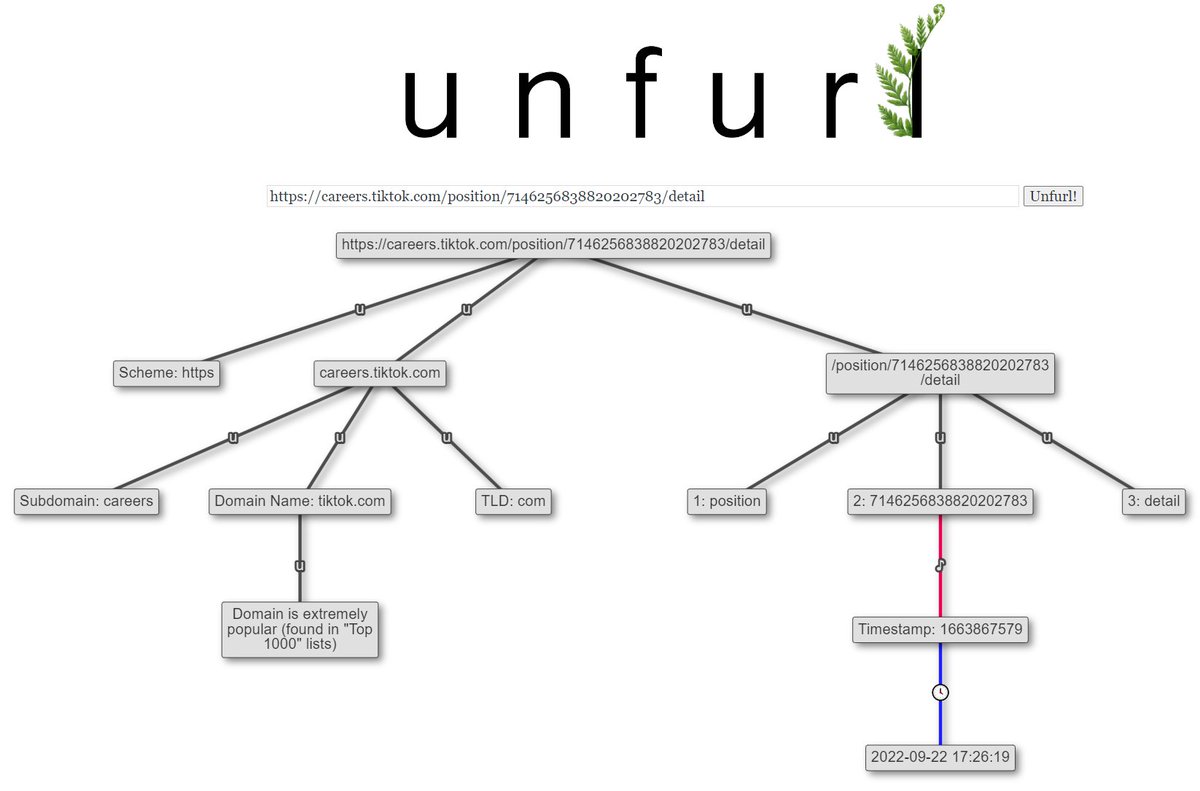
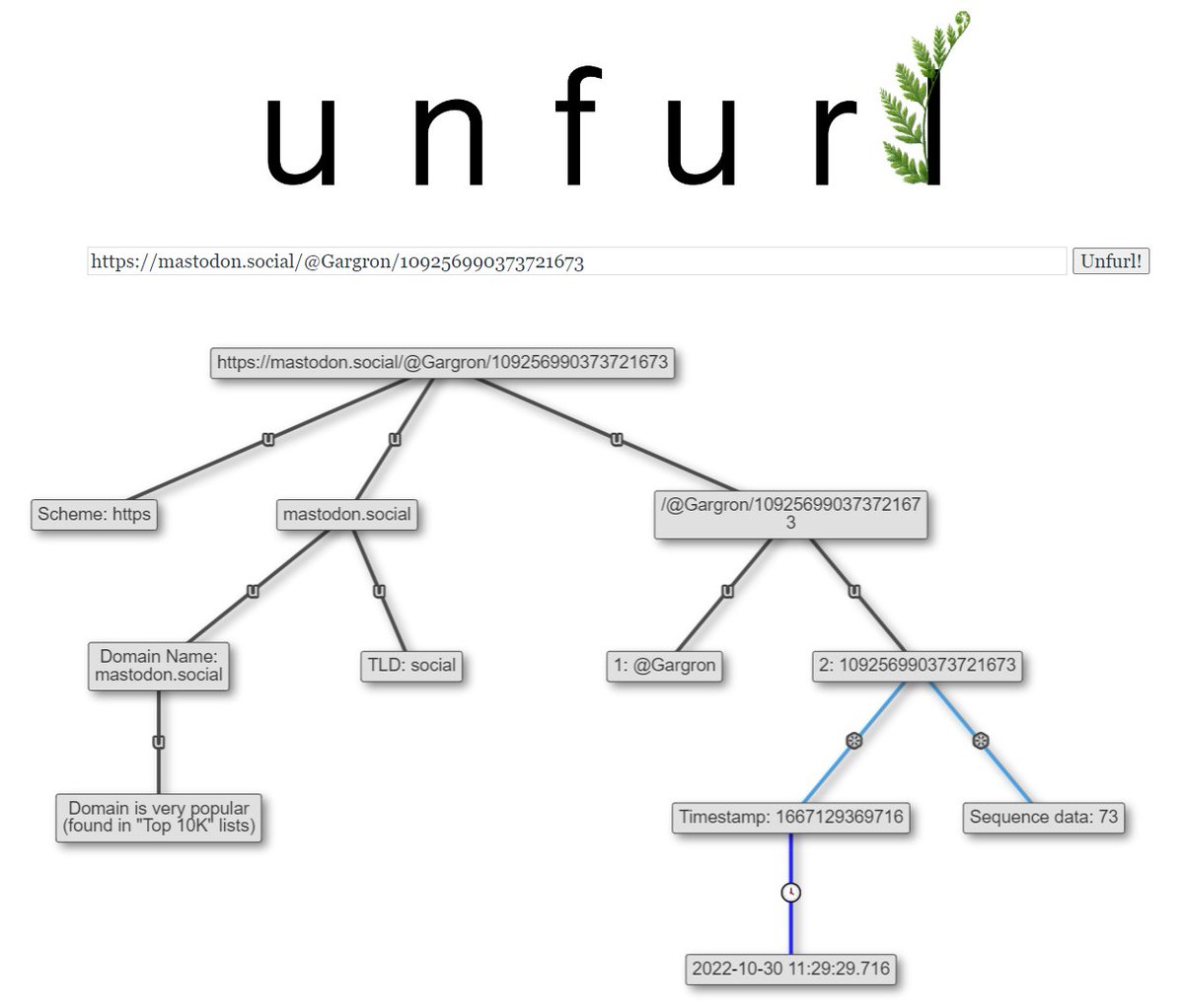
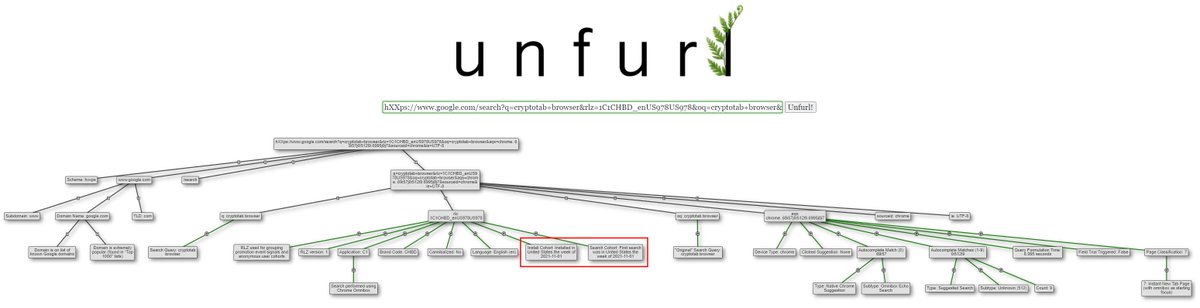
On browser forensics in #DFIR: In news.sophos.com/en-us/2022/04/…, just from the URL we can see the attackers installed Chrome the week of 2021-11-01. So much interesting stuff in URLs! Unfurl 🔗: dfir.blog/unfurl/?url=hX… h/t Phill Moore for the article and lots of nice Google research

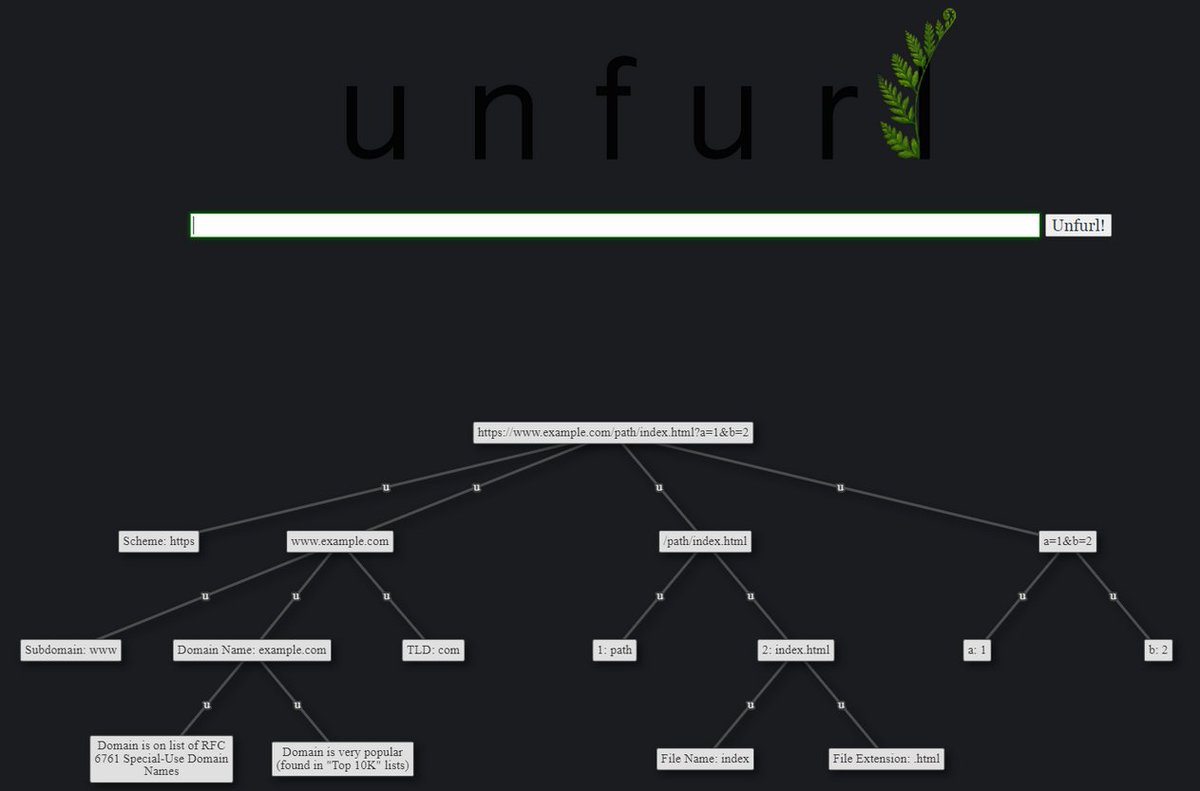
If you need to pull out all the data in complicated URLs, Try the excellent Unfurl tool to extract and visualize each bit in the URLs. dfir.blog/unfurl/ github.com/obsidianforens… Ryan Benson #OSINT #DFIR #BlueTeam #ThreatIntel #intelligence #ThreatHunting #infosec










We are reviewing our MISP (@[email protected]) warning lists and we are looking for a maintained list of hosts which are domain parking. Do you know someone doing such thing? or should we start to build one from scratch? #threatintelligence