
Mike Schiessl
@schiesslmike
ID: 1346833714219802629
06-01-2021 14:59:56
24 Tweet
2 Followers
15 Following

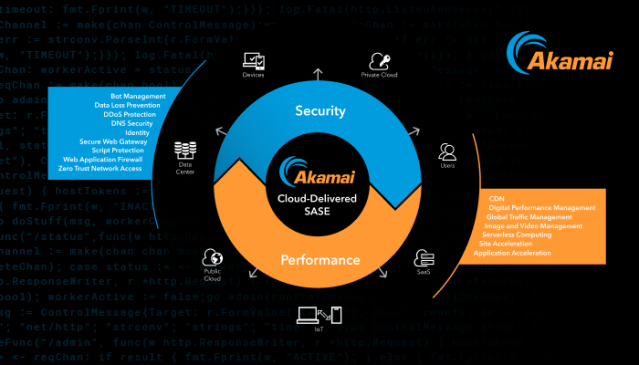
Deliver security controls at the edge, as close to the end-user as possible. Learn more about ZTNA, SWG, and securing the workforce. Akamai Technologies #ZeroTrust bit.ly/3k6TYML

With the #Vaccine Edge, Akamai Technologies is providing vaccination registration websites with much-needed delivery, security, and waiting room logic. Learn more. iTWire - Latest News #cybersecurity bit.ly/3dWNvD1


With the #Vaccine Edge, Akamai Technologies is providing vaccination registration websites with much-needed delivery, security, and waiting room logic. Learn more. iTWire - Latest News #cybersecurity bit.ly/3sub5Ls


#Credentialstuffing attacks are on the rise across all industries. Akamai Technologies reported that 60% of these attacks targeted retail, travel, and hospitality businesses. Read more. Infosecurity Magazine Phil Muncaster #cybersecurity bit.ly/3rmchAx


With a newly developed algorithm called Morton, Akamai Technologies's Hen Tzabans shows how UEBA solutions detect devices that are engaging in malicious DNS behavior. Read more. #cybersecurity bit.ly/2OpByuH

Is your MFA solution just security theater based on current threats? Join this session to learn how to select the right MFA solution for you. Akamai Technologies #cybersecurity bit.ly/2MPVoyU


Akamai continues to focus on innovation by launching Cohort 2 of the Akamai Technologies Startup program. Learn more. bit.ly/2PKqObc


Learn how to measure the different types of MFA solutions on the market based on industry best practices during this live session. Akamai Technologies #cybersecurity bit.ly/2OXPuN6


Akamai MFA delivers the benefits of FIDO2-based MFA, without the cost and complexity of physical #security keys. Upgrade to secure, frictionless MFA. Akamai Technologies bit.ly/3vt3WgC

There’s no doubt that MFA reduces the risk of account takeover. But it’s become apparent that MFA can be bypassed. Upgrade your MFA. Akamai Technologies bit.ly/3r0RNfo

New Akamai Technologies MFA enables enterprises to quickly deploy FIDO2 #authentication without the need to deploy and manage hardware security keys. Read more. Help Net Security #cybersecurity bit.ly/2Q87JQf


While CISA's warning about the Pulse #VPN vulnerability is top of mind, this is really just the latest example of a pattern that has repeated itself for the past 2 years. Find out more from Akamai Technologies's Patrick Sullivan. #ZeroTrust bit.ly/3nPidkw


Intelligently augment human decision-making with machine learning for faster, more trustworthy security outcomes. Learn more. Akamai Technologies bit.ly/2Shl7TK


Learn why Akamai Technologies's Robert Blumofe believes that all network access should be treated as remote access, even when in the office. #ZeroTrust bit.ly/3flJUhT


Discover how to create an Akamai Technologies Application Security configuration using Postman and interfacing directly with the Application Security #API. Watch here. Akamai Developer bit.ly/2WFxhrz

Prevent, mitigate, and recover from ransomware attacks with Zero Trust micro-segmentation. Learn more with Ariel Zeitlin, co-founder of Guardicore, now part of Akamai Technologies. Register here. #cybersecurity bit.ly/3x67yXg


App & #API Protector makes it easier for IT teams to embrace DevSecOps best practices via a converged web application and API (WAAP) service. Learn more. Akamai Technologies DevOps.com #cybersecurity bit.ly/3CBWDWn

Join us on December 14 as we cut through the hype and show you how #microsegmentation should fit into your #cybersecurity strategy. Register here. Akamai Technologies bit.ly/3d2SbFQ


Hear why microsegmenting a Kubernetes cluster is crucial in our live webinar. Register today. Akamai Technologies Richard Meeus #microsegmentation #ZeroTrust bit.ly/3ktGtb1
