p0 Labs
@p0labs
Cloud Threat Research and Detection Engineering is our Priority Zero (p0) at Permiso Security.
ID: 1506319063261368328
https://permiso.io/blog 22-03-2022 17:18:23
34 Tweet
106 Followers
32 Following





🔖 Cloud Cred Harvesting Campaign A credential harvesting campaign targeting cloud infrastructure. The majority of the victim system were running public facing Juptyer Notebooks. From Permiso Security permiso.io/blog/s/christm…

🔖 SES-pionage What do attackers do with exposed AWS access keys? This blog looks inside AWS SES to give deeper insights into the service, why & how its targeted and how to detect it. From Permiso Security permiso.io/blog/s/aws-ses…

Compromised Access Keys aren't the only vector for #cloud Attacks. Checkout our (Permiso Security ) latest article where we detail an ongoing wateringhole attack targeting #AWS management console users via #google ads. permiso.io/blog/s/waterin…

Meet the p0 Labs team: #pixelart version. #FollowFriday Permiso Security @Security_Nate Daniel Bohannon Bleon Proko Opie



Cloud Apps Still Demand Way More Privileges Than They Use darkreading.com/tech-trends/cl… via Dark Reading Permiso Security #CSPM #AppSec

Last week we Permiso Security wrote an article permiso.io/blog/s/waterin… speaking to a #google ads phishing campaign targeting #brazilian #AWS users. Tom Hegel discovered the next phase of the attackers campaign, catch the details from the SentinelOne team sentinelone.com/blog/cloud-cre…

Keep an eye out for usage of deprecated #AWS policies. Bleon Proko makes his Permiso Security p0 Labs blog debut talking about the dangers of the deprecated policy AmazonEC2RoleforSSM permiso.io/blog/s/depreca…

Here Permiso Security the focus is on detection of #identity and #cloud threat activity. #Detection can be an art form with various methodologies. In this article we describe our approach to detection using AndroxGh0st and GreenBot as an example! permiso.io/blog/s/approac…

New joint release with our friends at Permiso Security / p0 Labs 👇 AWS-Targeting Cred Stealer Expands to Azure, GCP 💜 s1.ai/cloudcreds 💜 permiso.io/blog/s/agile-a… Alex Delamotte 1aN0rmus Daniel Bohannon #ThreatIntel

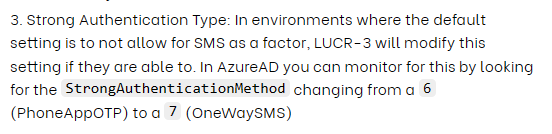
Beware of LUCR-3! 🚨 Threat actor that overlaps with Scattered Spider, Oktapus, UNC3944, & STORM-0875, they exploit IDPs for initial access & aim to steal IP for extortion. They use victims' tools and evade detection with expertise. Permiso Security permiso.io/blog/lucr-3-sc…

Excellent 🆕blog from Permiso Security on the most disruptive criminal intrusion set we're all working on. Blog details evasive techniques scattered across SaaS & multi-cloud environments.



An area needing attention for protecting modern applications against threats👇 -access via IDP identities -LUCR-3 uses SaaS applications to learn how the victim organization operates and how to access sensitive information." #cloudsecurity #iam #sspm #appsec Permiso Security