Nekrom
@nekrom__
Bug Bounty & Red Teaming Tips and Tricks 💻 #Cybersecurity #BugBounty #BugBountyTips #RedTeam
ID: 968950145046990848
28-02-2018 20:44:51
349 Tweet
260 Followers
846 Following









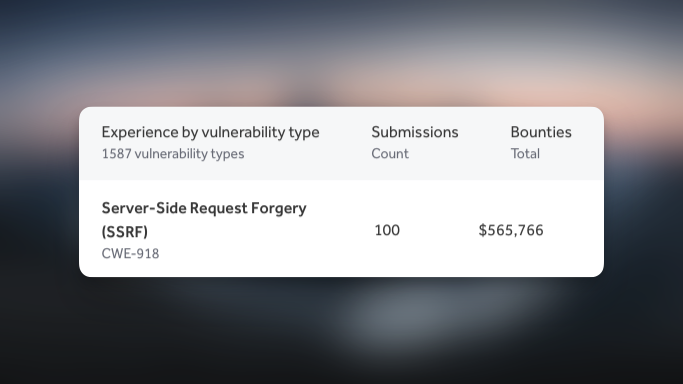
How do we turn bad SSRF (blind) into good SSRF (full response)? The Assetnote Security Research team at Searchlight Cyber used a novel technique involving HTTP redirect loops and incremental status codes that leaked the full HTTP resp. It may work elsewhere! slcyber.io/assetnote-secu…




Sometimes, SQL injection is still possible, even when prepared statements are being used. Our researcher hashkitten has written up a blog post about a novel technique for SQL Injection in PDO’s prepared statements: slcyber.io/assetnote-secu…

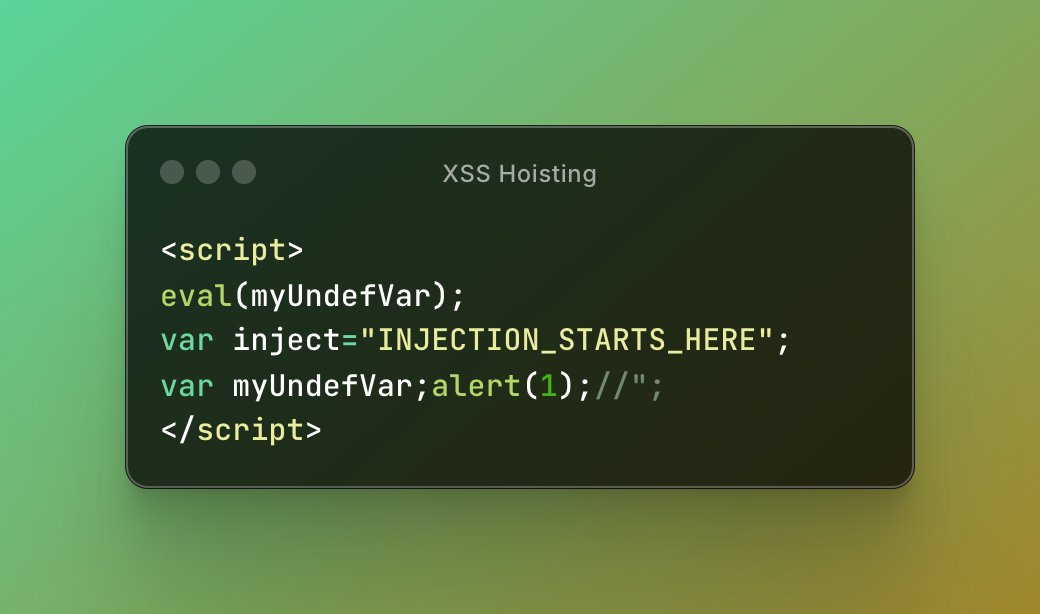
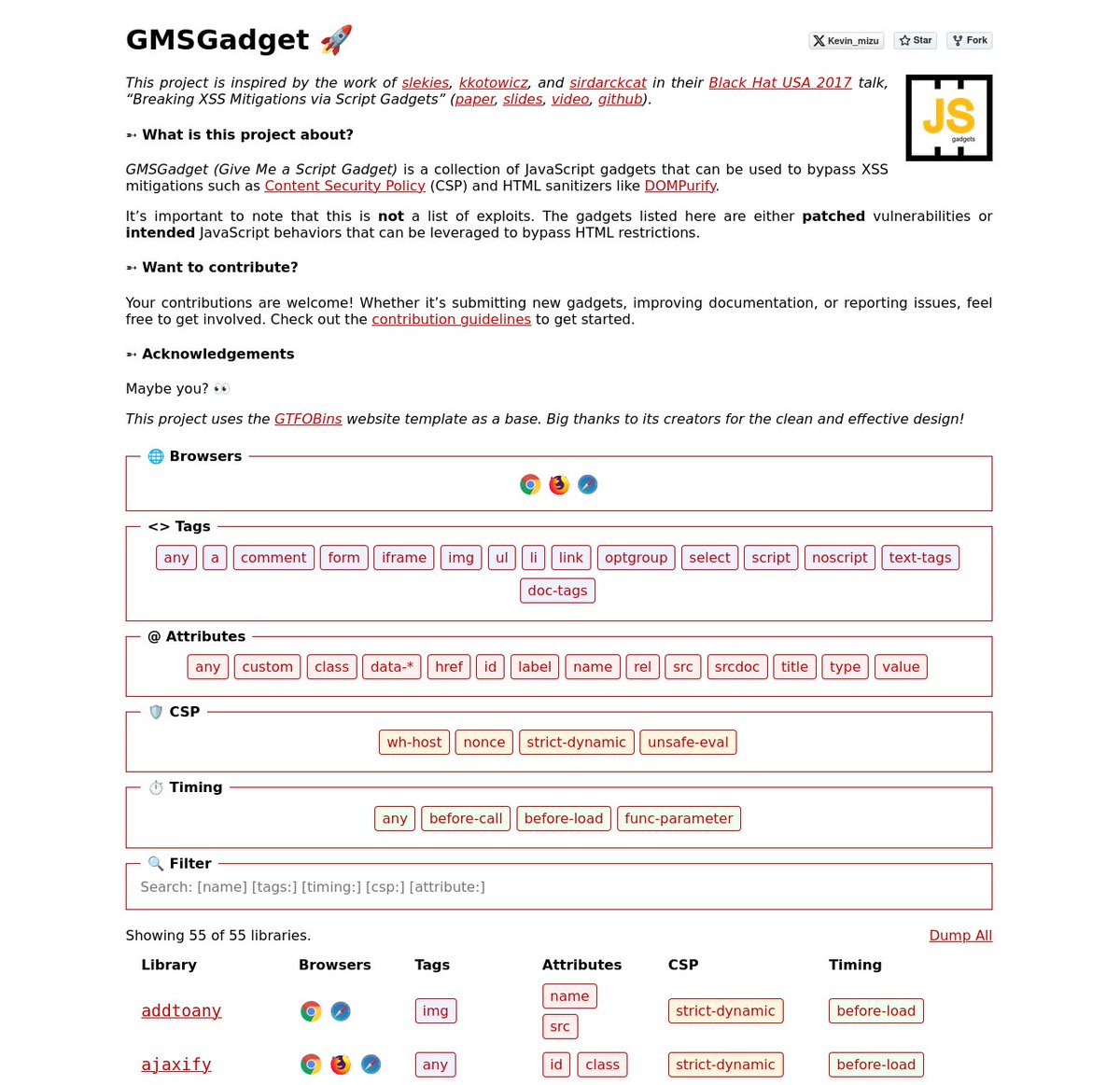
I'm happy to release a script gadgets wiki inspired by the work of Sebastian Lekies, koto, and Eduardo Vela in their Black Hat USA 2017 talk! 🔥 The goal is to provide quick access to gadgets that help bypass HTML sanitizers and CSPs 👇 gmsgadget.com 1/4



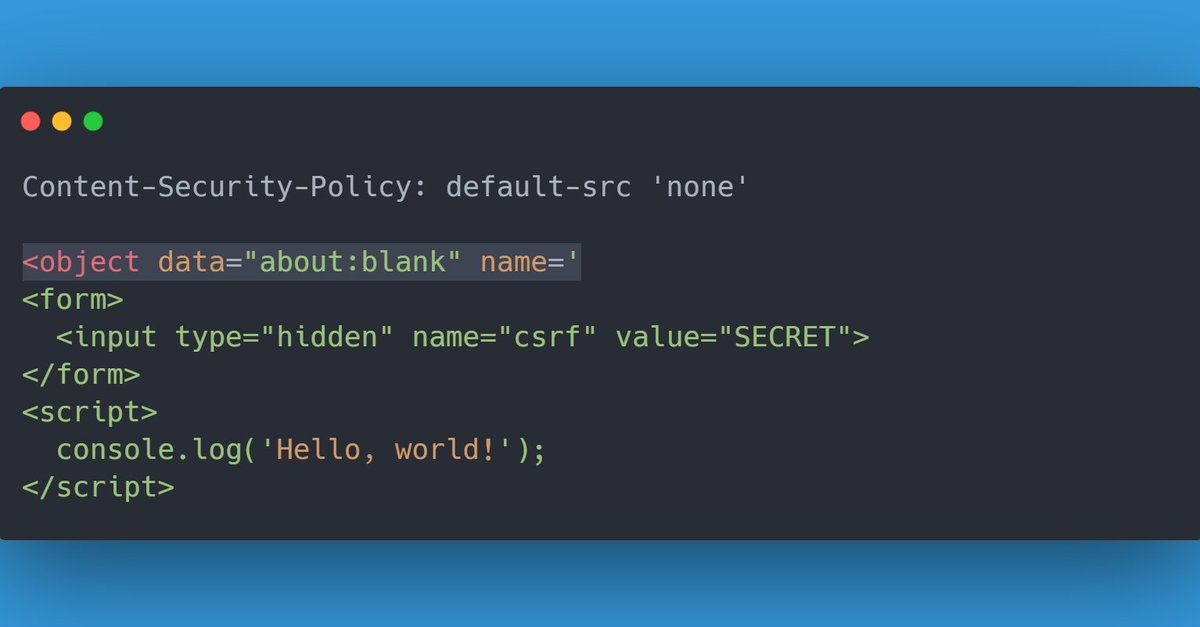
While playing a challenge by Salvatore Abello, I found a pretty interesting way to exploit Dangling Markup with a strict CSP. All you need is an <iframe>, <object> or <embed> set to about:blank, with a dangling name= attribute. This vulnerable page should be iframable.