Martin Gallo 🇦🇷 💚✊🏾🚀
@martingalloar
InfoSec Leader/Innovation | 👨🏾💻PdM @HYPRCorp | 🙆Co-org @TandilSec | 🧐CFP @ekoparty | ✊Knowledge sharing and community building | 🏀#12 | 🗨️Words are mine
ID: 17143251
https://www.linkedin.com/in/mgallo/ 03-11-2008 23:06:51
2,2K Tweet
1,1K Takipçi
500 Takip Edilen


Balance de 4 años al frente de la Fundación Sadosky y otros 10 un poco más atrás. Terminó una etapa en la Fundación Sadosky y quiero compartir algunas reflexiones y un balance de lo realizado. bit.ly/4k1g54o








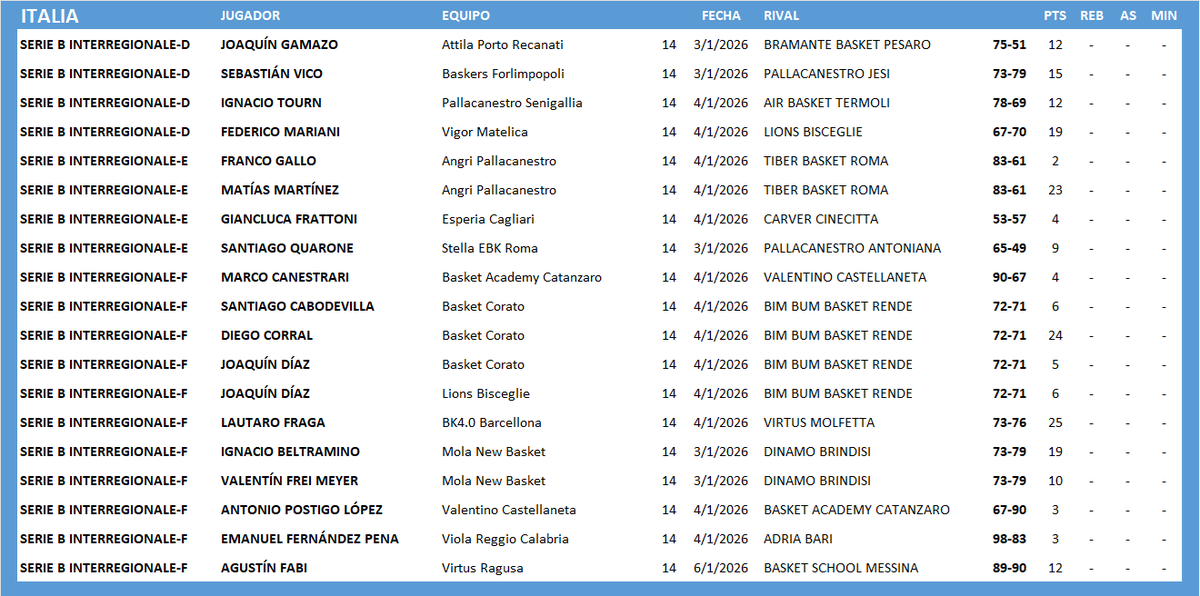
#ArgentinosXelMundo ITALIA 🇮🇹 SERIE B INTERREGIONALE (2/2) joaquin gamazo Nacho Tourn Fede Mariani Gianluca Frattoni leo cecchi Lautaro Fraga Agustin Fabi



#ArgentinosXelMundo ITALIA 🇮🇹 SERIE B INTERREGIONALE (2/2) joaquin gamazo Nacho Tourn Fede Mariani Gianluca Frattoni leo cecchi Lautaro Fraga Emanuel Fernandez Agustin Fabi
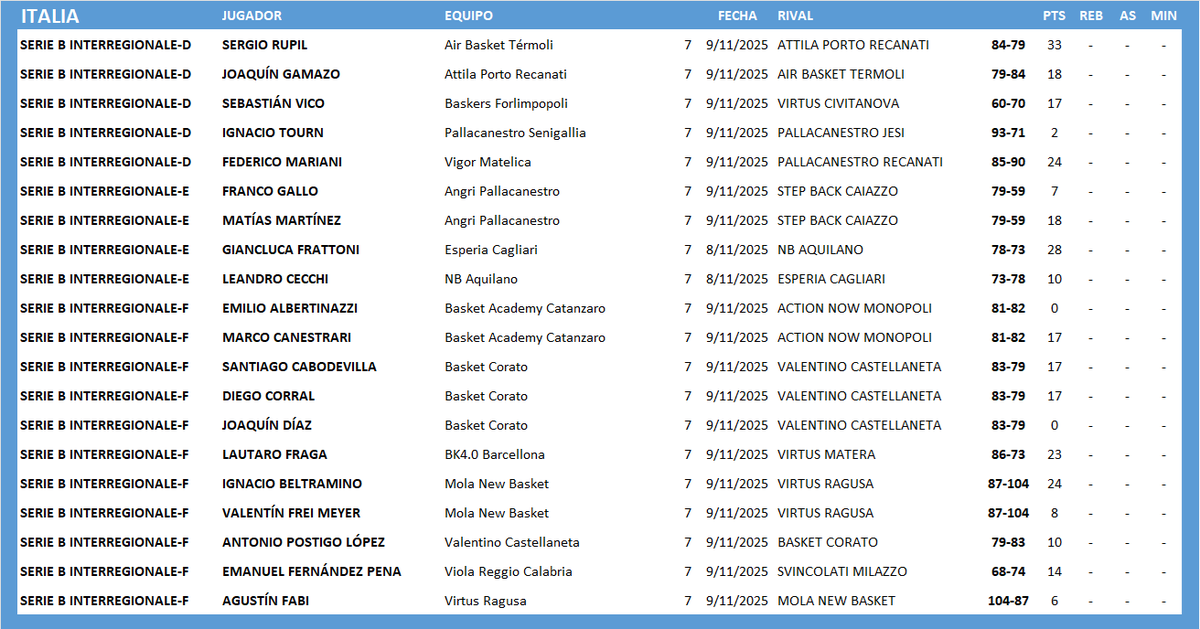


#ArgentinosXelMundo ITALIA 🇮🇹 SERIE B INTERREGIONALE (2/2) joaquin gamazo Nacho Tourn Fede Mariani Gianluca Frattoni leo cecchi Lautaro Fraga Emanuel Fernandez Agustin Fabi


#ArgentinosXelMundo ITALIA 🇮🇹 SERIE B INTERREGIONALE (2/2) joaquin gamazo Nacho Tourn Fede Mariani Gianluca Frattoni Lautaro Fraga Emanuel Fernandez