First Dan Kaminsky Fellow | Security Researcher for the OSS Ecosystem | Speaker | Dropper of 0days (Responsibly) | @GitHub Star ⭐️ | Opinions=Mine | He/Him
ID: 146534354
https://stars.github.com/profiles/jlleitschuh/ 21-05-2010 17:38:07
2,2K Tweet
3,3K Followers
604 Following


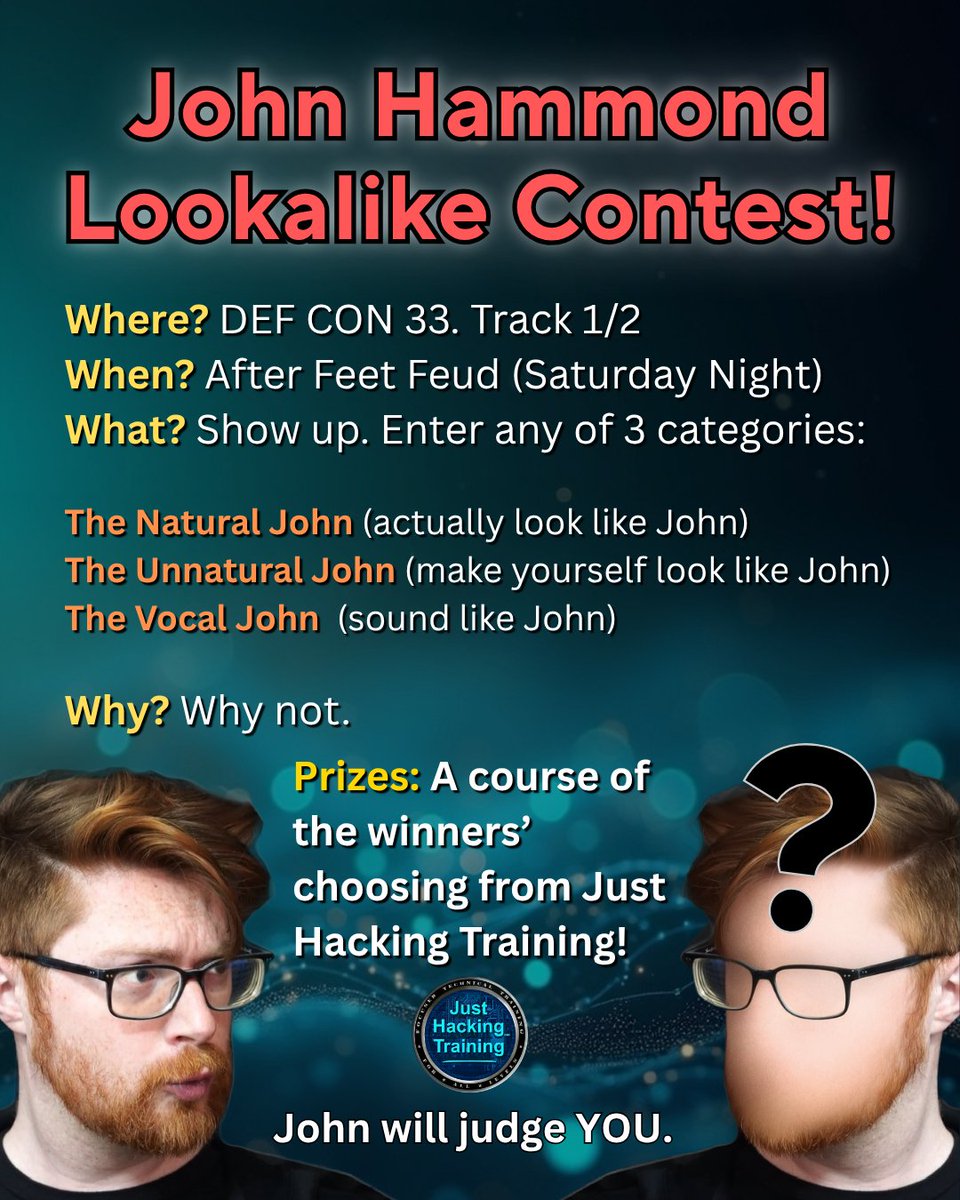
Do you look like John Hammond? Do you sound like John Hammond? Heck, can you just make yourself look like John Hammond? Come along to Feet Feud (hackertracker.app/event/?conf=DE…) at DEF CON 33 and compete with other Johnalikes to win prizes. The judge? John Hammond of course. 🤓


How is this blocked? Cloudflare this vulnerability impacts a localhost server Unless you've released a new locally running firewall that I didn't hear about, I'd say that you're customers are probably not safe against this This remains a critical RCE vulnerability

dawg, BobDaHacker 🏳️⚧️ | NB compromised McDonalds by finding one of their endpoints and ... REGISTERING AN ACCOUNT. That's all it took. It then sent a plaintext password via email. McDonalds did however apparently fix the problem when they reported it to them.





