Samia Akter
@incognito_sami
𝓘 𝓯𝓮𝓵𝓵 𝓲𝓷 𝓵𝓸𝓿𝓮 𝔀𝓲𝓽𝓱 𝓬𝔂𝓫𝓮𝓻𝓼𝓮𝓬𝓾𝓻𝓲𝓽𝔂.👩🏻💻o(〃^▽^〃)o
ID: 1296084603497717761
19-08-2020 14:04:06
377 Tweet
611 Followers
1,1K Following




You asked and we answered... Because of the interest in our merch, we've decided to run a giveaway! We're offering merch bundles to 10 lucky winners (items may vary to those shown). To enter: 🛡️ Follow us and CySec Careers 🛡️ Retweet this tweet Worldwide. Closes Jan 5, 2024







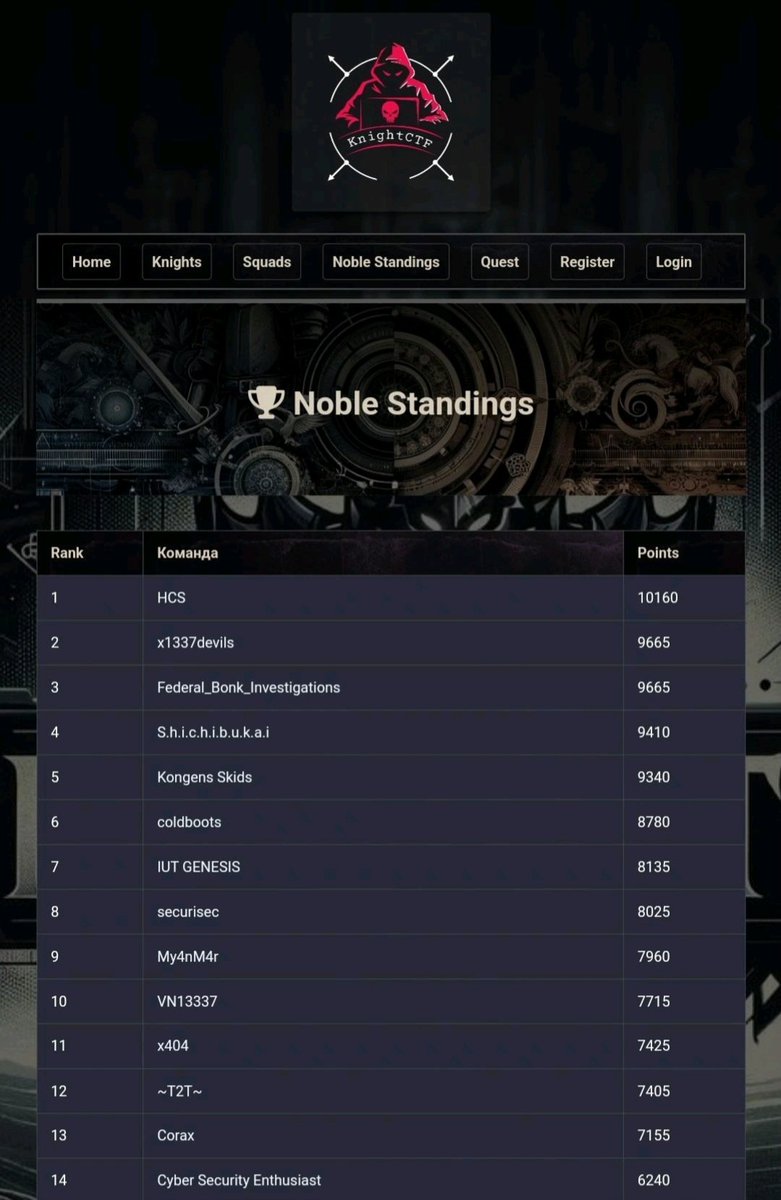
Excited to announce that our team Federal_bonk_Investigations🇧🇩 achieved – 3rd position in the International CTF! 🏆 Grateful to my teammates for their dedication specially Kazi Ashikur Rahman vaiya🫡Thanks to Knight Squad for organizing a competitive contest. #ctf #cybersecurity #knightctf2024 #fbictf