
dmpdump
@g60930953







Thread Execution Hijacking is one of the well-known methods that can be used to run implanted code. In this blog we introduce a new injection method, that is based on this classic technique, but much stealthier - Waiting Thread Hijacking. Read More : research.checkpoint.com/2025/waiting-t…





![dmpdump (@g60930953) on Twitter photo #WinOS #ValleyRAT
DLL Hijacking
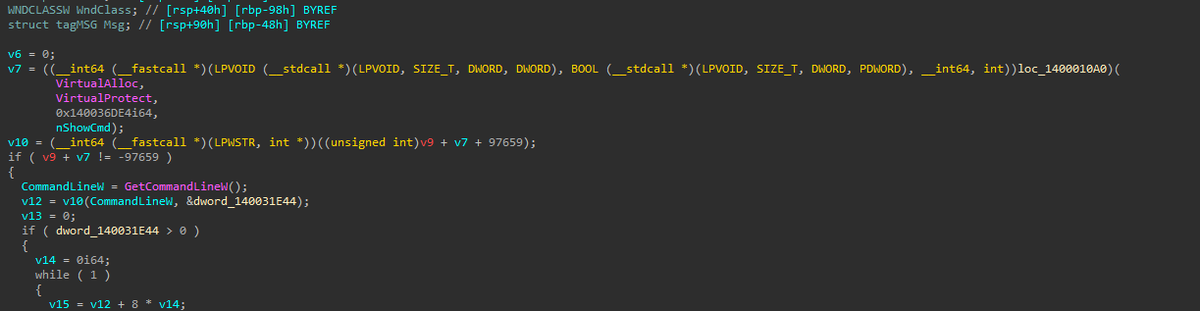
Shellcode decryption + EnumFontsW callback function
8010.helloqu[.]com:7777
8010.helloqu[.]com:80 #WinOS #ValleyRAT
DLL Hijacking
Shellcode decryption + EnumFontsW callback function
8010.helloqu[.]com:7777
8010.helloqu[.]com:80](https://pbs.twimg.com/media/GmE-OPCXwAAJYy_.png)
