Elad Ernst
@eladernst
Cyber Security Researcher at
@blockaid_
ID: 1155440097526996998
28-07-2019 11:29:21
471 Tweet
764 Followers
316 Following





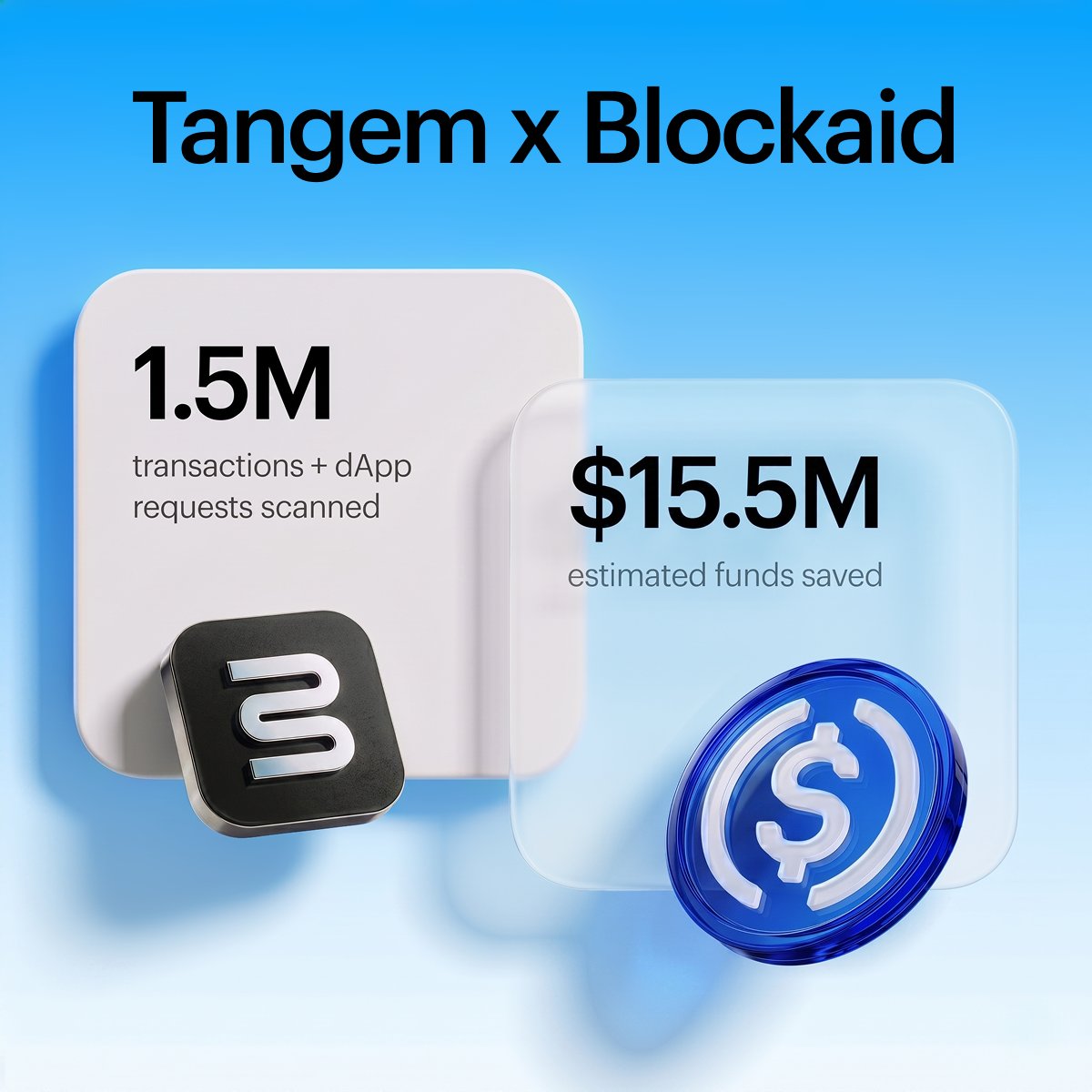
Update: Great news. Thanks to support from MystenLabs.sui and Sui Foundation all users will be made whole ZERO losses for anyone. Aftermath will be up and running again soon. Thank you to both teams and to Blockaid for the rapid response. For clarity: this was not a Move


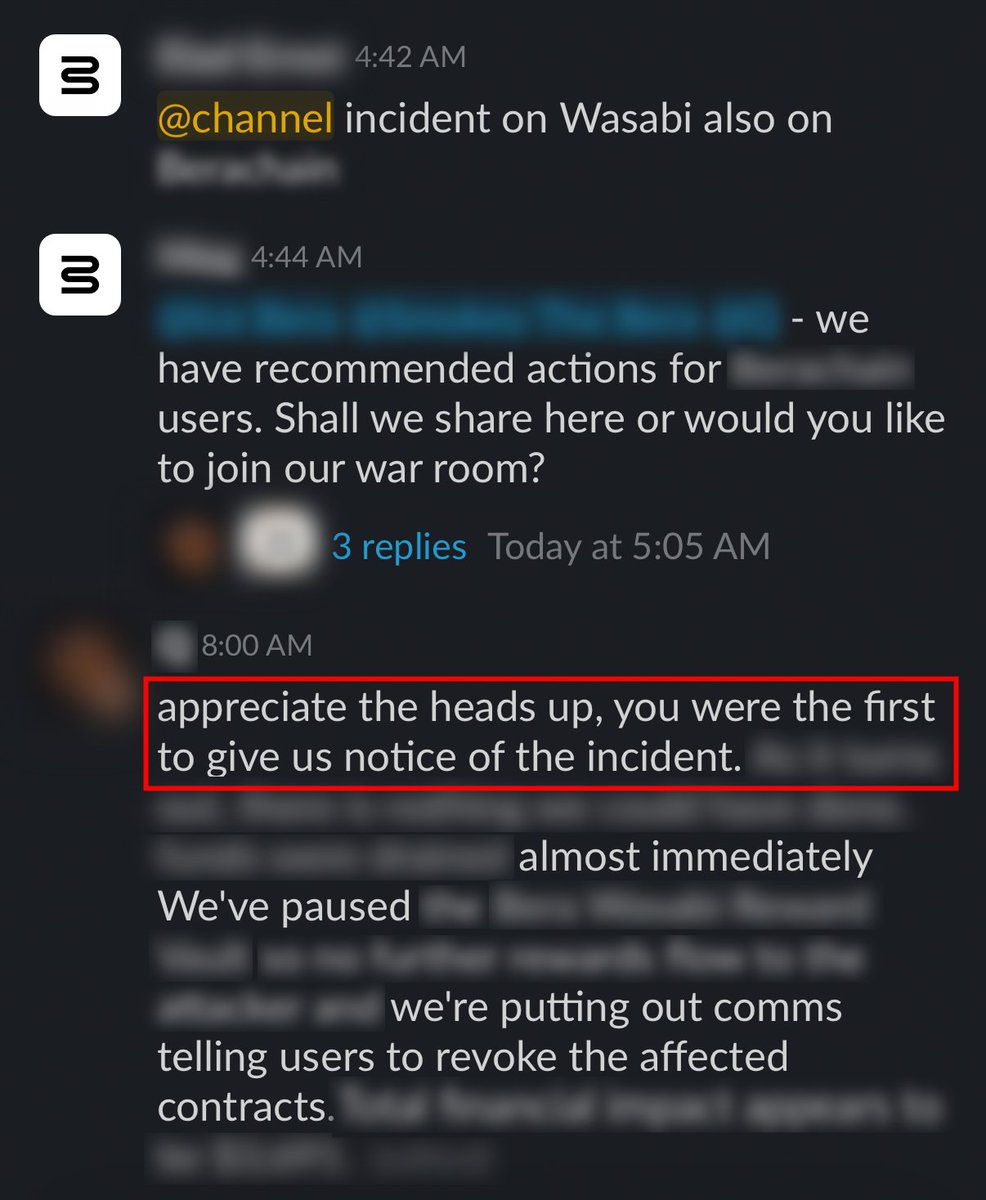
🚨 Blockaid's exploit detection system identified an on-going admin-key compromise exploit on Wasabi Protocol 🟢 across Ethereum and Base. The Wasabi: Deployer EOA was used to grant ADMIN_ROLE to an attacker helper contract, which then UUPS-upgraded the perp vaults and LongPool to