w4rd4wg
@donxaridis
g0t r00t?
ID: 42422301
25-05-2009 15:16:09
3,3K Tweet
561 Followers
5,5K Following











.Activision was breached December 4th, 2022. The Threat Actors successfully phished a privileged user on the network. They exfiltrated sensitive work place documents as well as scheduled to be released content dating to November 17th, 2023. Activision did not tell anyone.


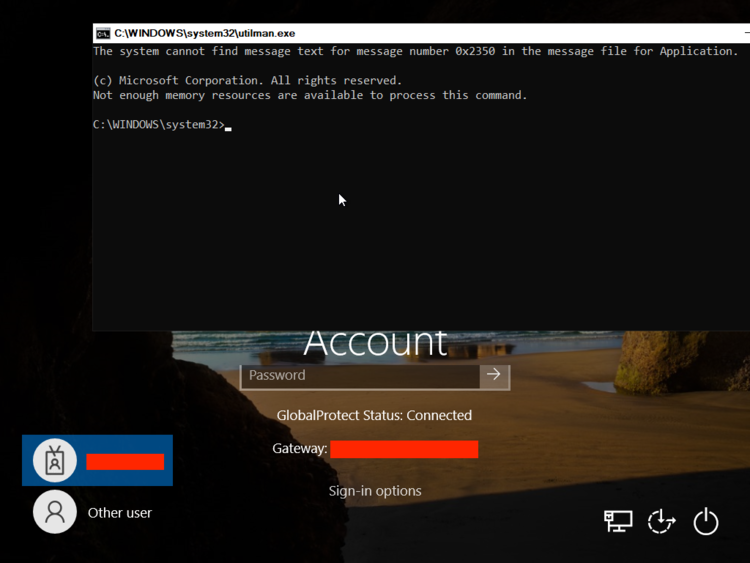
Releasing a Windows 11 LPE exploit by b33f | 🇺🇦✊ and I. Exploits CVE-2023-21768, a vuln in afd.sys. Blog post soon! github.com/xforcered/Wind…