Cyber Triage
@cybertriage
Digital Forensics and incident response software for endpoint investigation. Built by @sleuthkitlabs and Brian Carrier (@carrier4n6).
ID: 2916099598
https://www.cybertriage.com/ 11-12-2014 19:23:34
688 Tweet
4,4K Followers
394 Following

Velociraptor & Cyber Triage vs “DFIR World” attacks Learn from experts, Mike Cohen and Brian Carrier, how this integration can streamline your investigations. Join us on July 31st, register here: register.gotowebinar.com/register/12891…



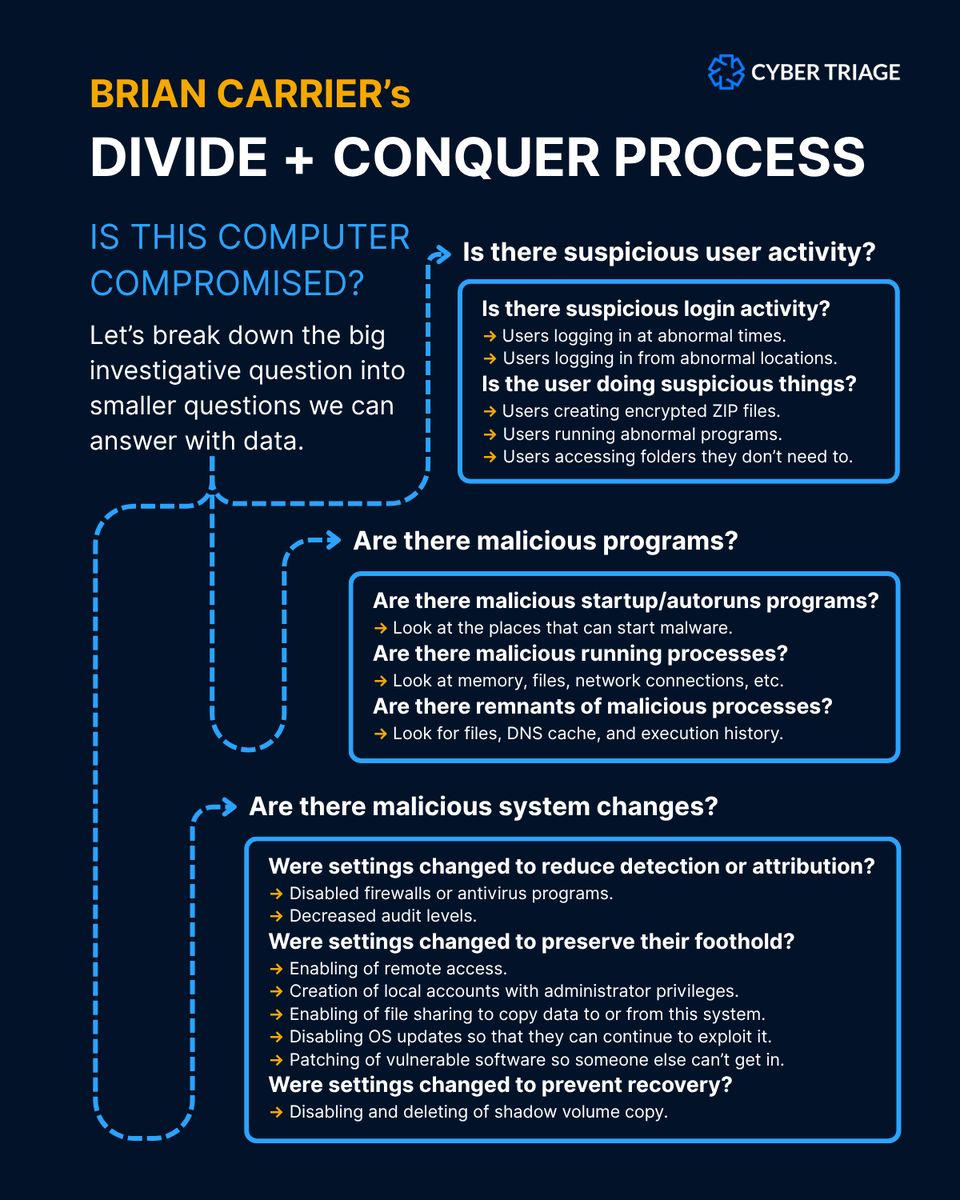
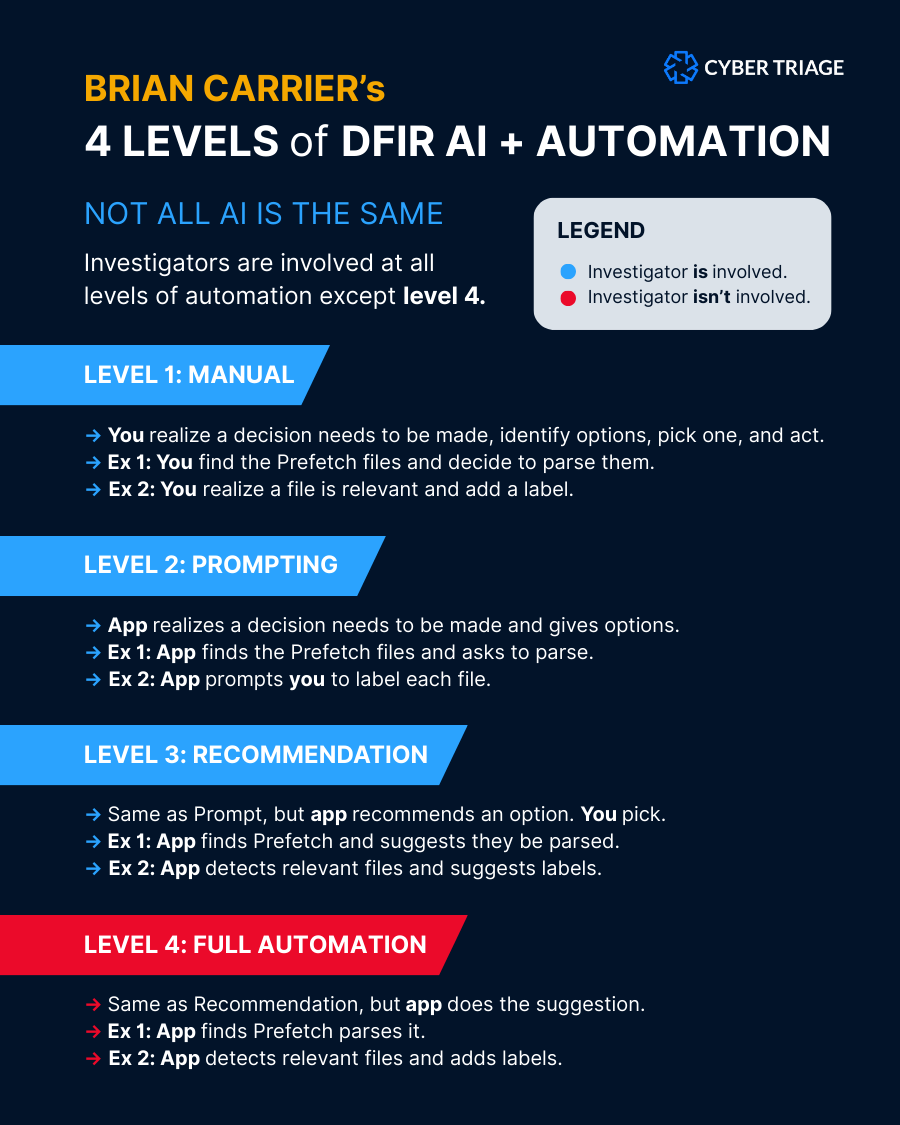
Understand investigation automation. Brian Carrier’s framework: cybertriage.com/blog/3-ways-to… You can test all 3 automation types with Cyber Triage. Trial copy: cybertriage.com/download-eval/



AI in digital investigations. Learn the basics from these 2 “guys”: → Brian Carrier → Sid Probstein Register now: attendee.gotowebinar.com/register/24378…



Learn AI basics in DFIR: → AI + LMMs in DFIR overview → When to apply AI to investigations → Live demo of LLM + Cyber Triage Join experts Brian Carrier and Sid Probstein tomorrow! Register: attendee.gotowebinar.com/register/24378…


New SOC DFIR Automation ⤵ CyberTriage 3.15 can automatically pull + analyze Defender data. See it live with Brian Carrier and Chris Ray on September 11. Register: attendee.gotowebinar.com/register/41993…




Free your mind: Automate your DFIR. Tomorrow, join Brian Carrier and Chris Ray as they demo the new Defender → Cyber Triage automation. Register: attendee.gotowebinar.com/register/41993…

RMMs: The Perfect Diguise. And attackers will get away with it, unless you learn to unmask them. Next Thursday, Mike Wilkinson will teach you just that. Register: attendee.gotowebinar.com/register/69551…





New DFIR Research: Pulseway (RMM) Abuse ⤵ Our team recently observed a threat actor using Pulseway for remote access and gaining full control of a system. Read Mike Wilkinson's research + investigation tips from the case: cybertriage.com/blog/dfir-next…