Crane Hassold 🏗
@cranehassold
Former Threat Intelligence lead at @AbnormalSec, @PhishLabs, | Former @FBI BAU analyst | @JMU alum | #phishing #BEC #threatintel
ID: 758651689662550016
28-07-2016 13:13:52
5,5K Tweet
2,2K Followers
901 Following

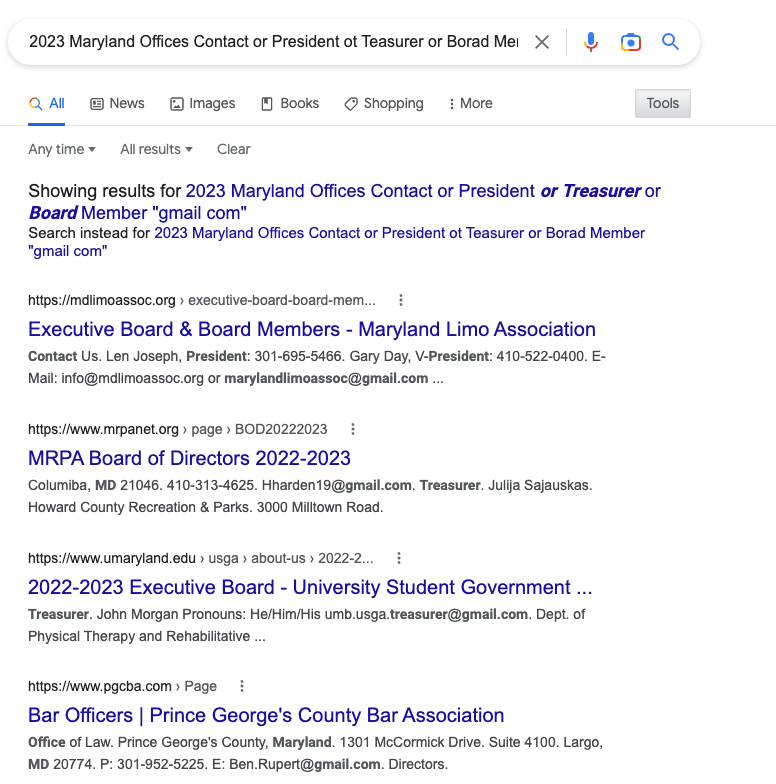
“We’ve been seeing a rapidly growing number of BEC attacks impersonating external third parties," Crane Hassold 🏗 cnn.com/2022/12/16/pol…



MeidasTouch What they were saying — trust me, I do this professionally.

Just because cyberattackers make use of the latest artificial intelligence system does not mean the attacks are harder to detect, for now, Rob Lemos (@roblemos just about everywhere) reports. bit.ly/3GXkl4R #ChatGPT #AI





Tune in Tuesday, Jan. 31, for our #RemoteSessions webcast on email attack vectors and how to stop them, with Crane Hassold 🏗, Director of Threat Intel for Abnormal AI. Register here: hubs.li/Q01zvkfs0


Published a new blog post today on multilingual #BEC attacks and how actors leverage Google Translate to target companies in 13+ languages. Includes details of two threat groups with my favorite names to date: Midnight Hedgehog and Mandarin Capybara! intelligence.abnormalsecurity.com/blog/midnight-…

One of the best parts about publishing research on a new threat group is seeing the graphics reporters use in their articles. Bravo Becky Bracken! 10 out of 10 for finding this graphic for Mandarin Capybara!