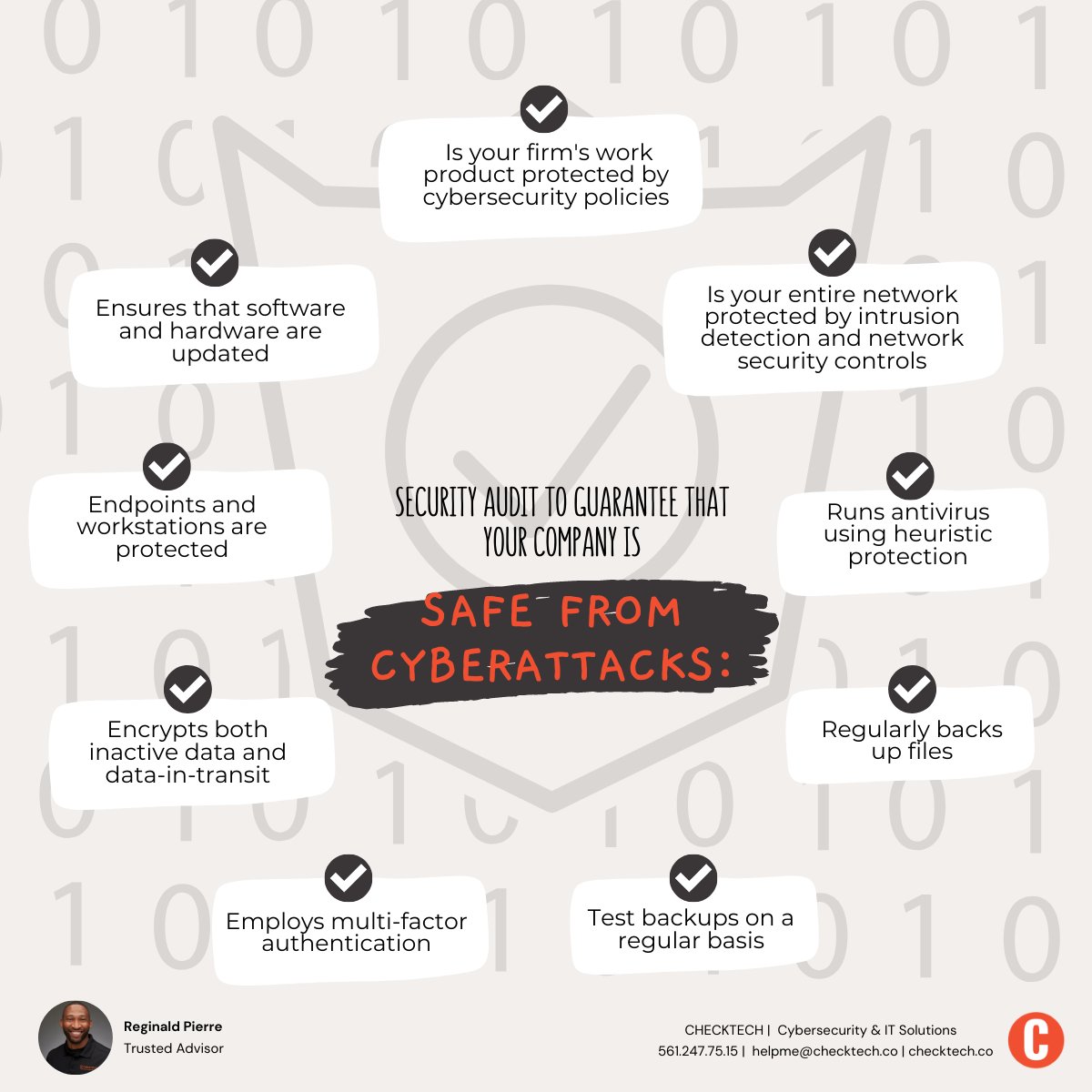
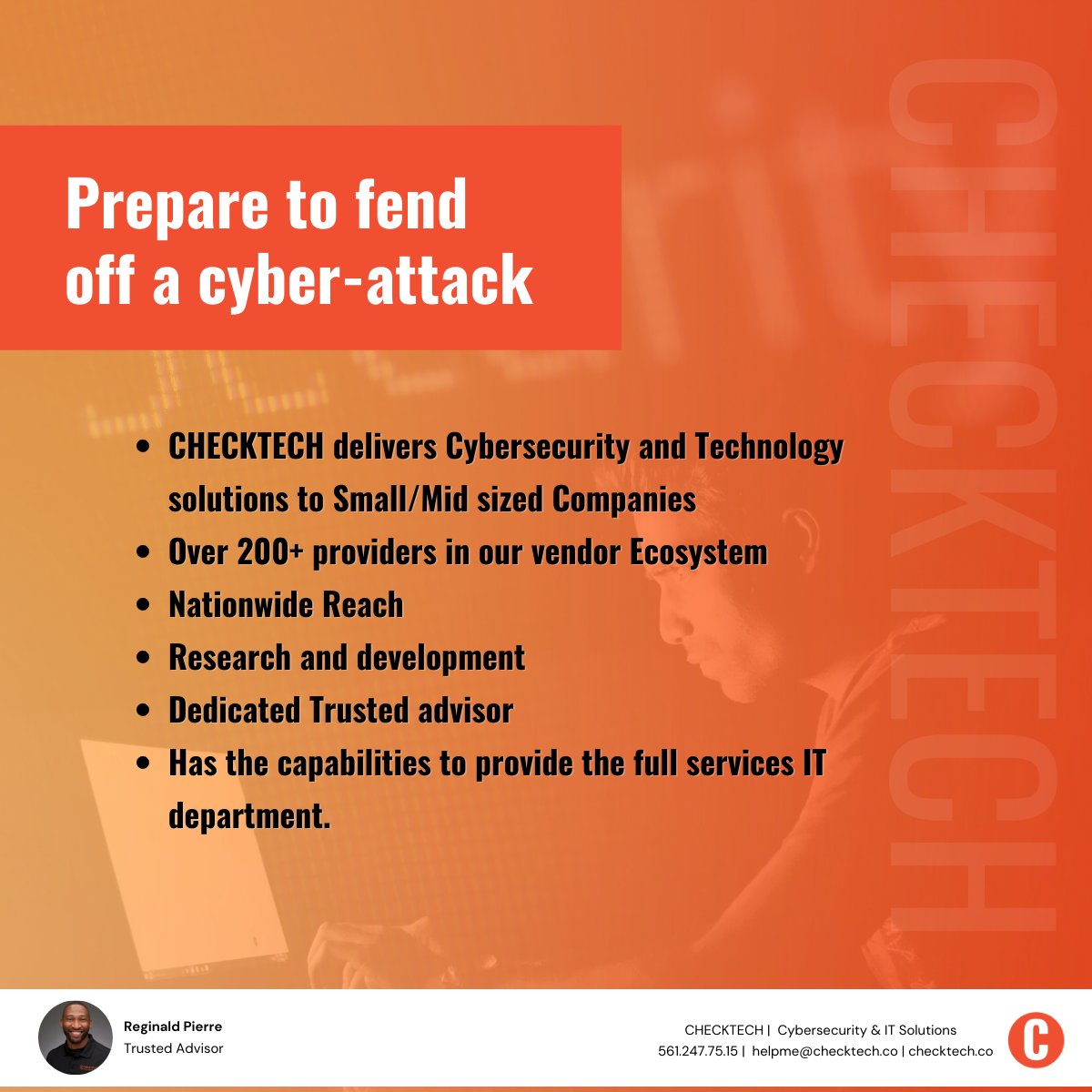
CHECKTECH™️
@checktechco
-Service Desk
-Cybersecurity
-Cloud
-Connectivity & Voice
-Office Equipment (Printers, Copiers, etc.)
-Web Development
ID: 1409516421286043649
http://checktech.co 28-06-2021 14:18:22
136 Tweet
45 Takipçi
1,1K Takip Edilen

CHECKTECH™️ What about folk already using #Windows11 Beta programs on hardware that wasn't supposed to be 'fully compatible' ?