Binarywishes
@binarywishes
Infosec.Ajumah Mama Bear. Army veteran. All opinions and comments are my own. @[email protected]
ID: 4813506614
25-01-2016 18:56:27
799 Tweet
279 Takipçi
704 Takip Edilen



Facebook finds new Android malware used by APT hackers - Bill Toulas bleepingcomputer.com/news/security/…


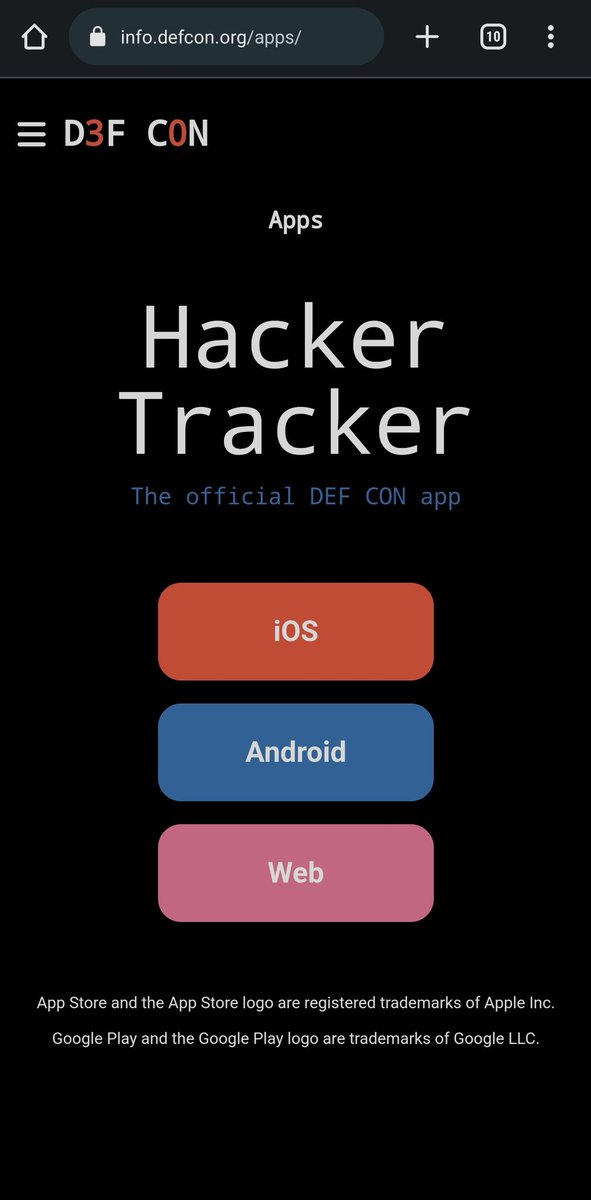
i started the DEF CON #HackerTracker project 10 years ago, and it makes me so happy to see it continue to grow and be supported 💙 kudos to SeThLaW (l4wke) advice Drew Stemen (@[email protected]) @dcib 🌈










We are actively researching claims of 0-day vulnerabilities in Microsoft Exchange Server. There are currently two 0-Day Initiative allocations for related vulns, with no known associated CVEs. We are tracking based on indications in this original document www-gteltsc-vn.translate.goog/blog/canh-bao-…

We confirm that iOS 16 does communicate with Apple services outside an active VPN tunnel. Worse, it leaks DNS requests. #Apple services that escape the VPN connection include Health, Maps, Wallet. We used Proton VPN and #Wireshark. Details in the video: #CyberSecurity #Privacy