BIC_Nairobi
@bic_nairobi
Blacks in Cybersecurity™ Official Nairobi Kenya Twitter! #LitLikeBic
ID: 1243995330460422147
https://www.blacksincyberconf.com/ 28-03-2020 20:16:39
55 Tweet
134 Followers
23 Following

UPDATE: we're looking for computer donations for our program. COVID19 has given us the opportunity to stock up & set up labs for our participating high schools in Kenya. You can also send in your donations via PAYBILL 8001920, Acc: CyDC Comps. cc Swift Intellect LTD @CyberSpaceKenya












The BIC Awards #BICA2021 are currently happening. Plenty of awesome people pushing for tech and Cyber Security in the Black Community globally. Blacks In Cybersecurity #ShareTheMicInCyber






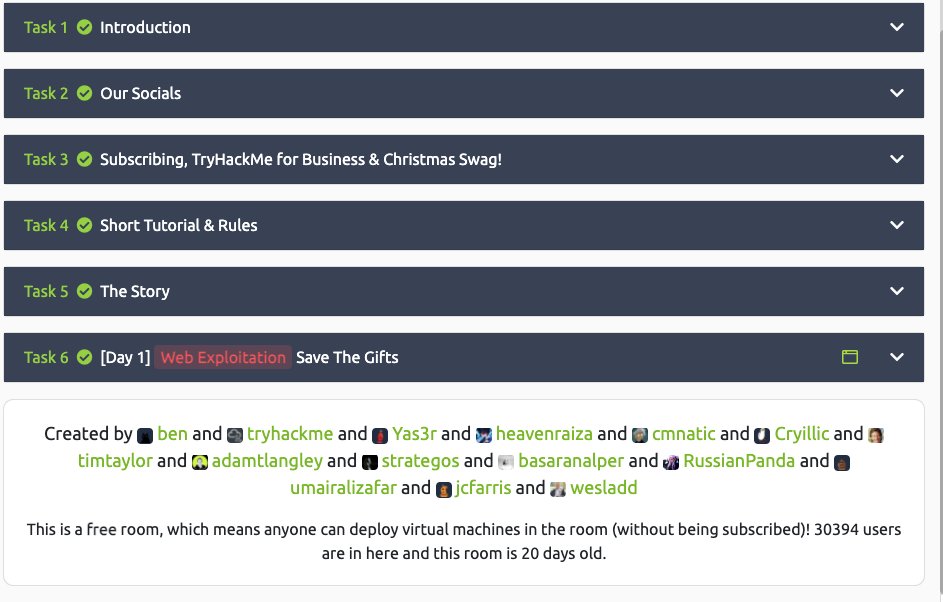
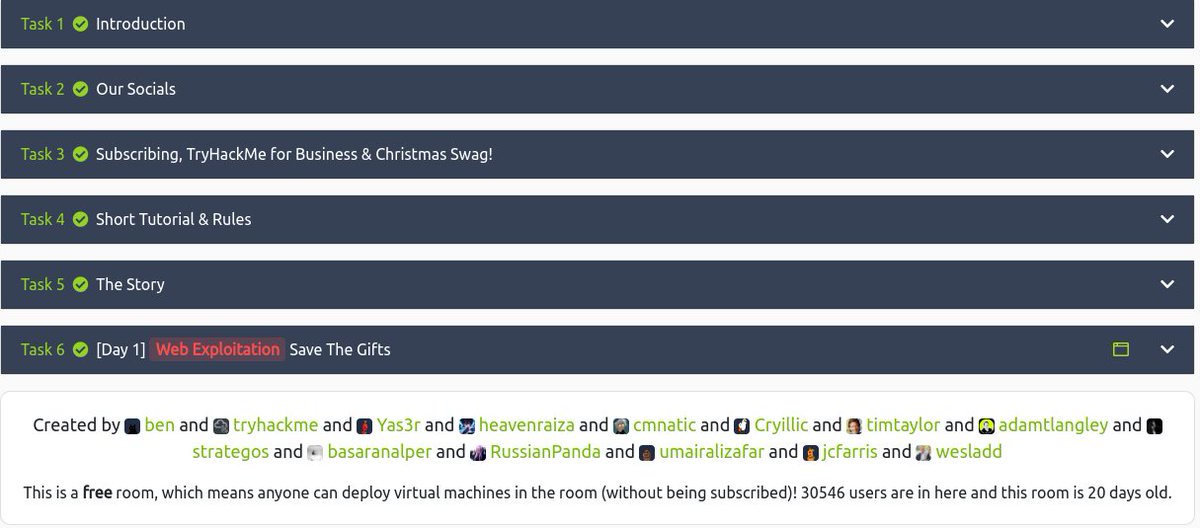
Day 8 of #AoC2021 from was a real bag of toys and tricks. Special Task from John Hammond and is a good log analysis and investigation test. Good to see SheHacks KE #SheHacks2025 article on Shellbags be used as material. Keep learning #Cybersecurity #THM #CTF