Anubhav Singh🇮🇳
@anubhavsingh_
Security Engineer @SecInnovation | @OwaspDkte chapter leader • CTF Player ⛳ • Bug Hunter 🧐 • Project Morya • Tea is ❤️ • Learn365 • eCPPTv2 • eWPTXv2
ID: 1203744416759869440
https://github.com/dn0m1n8tor 08-12-2019 18:33:53
6,6K Tweet
8,8K Followers
808 Following

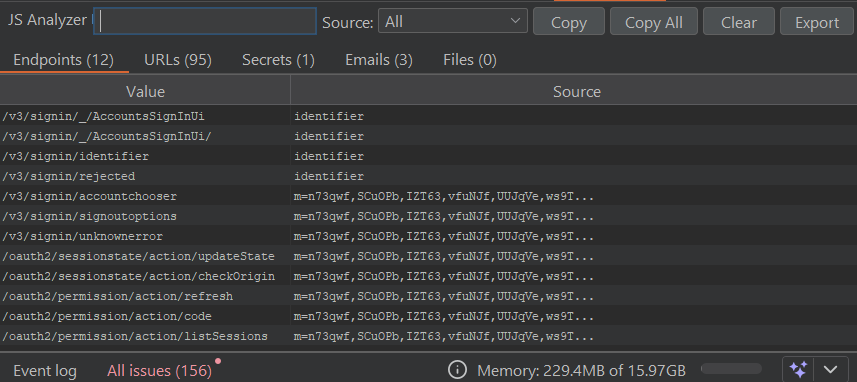
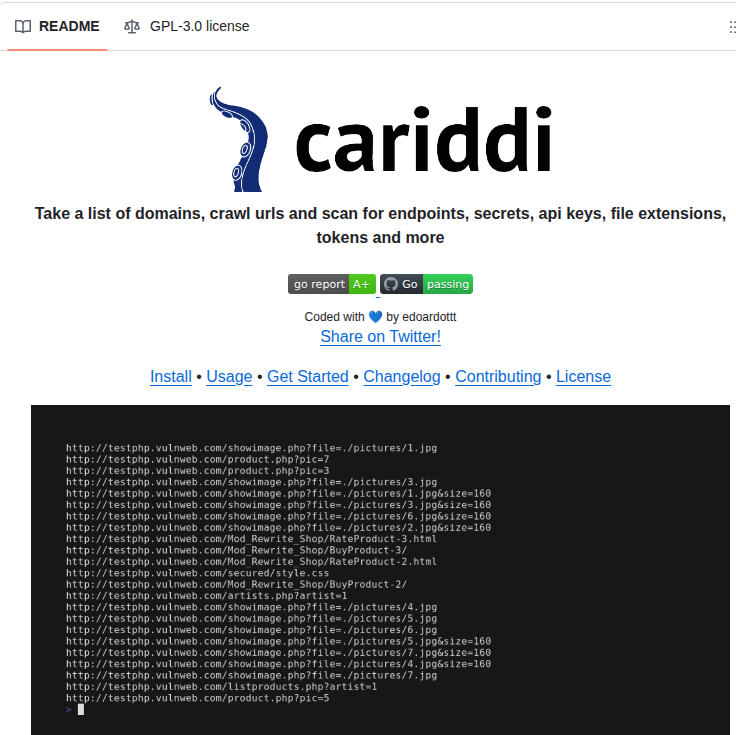
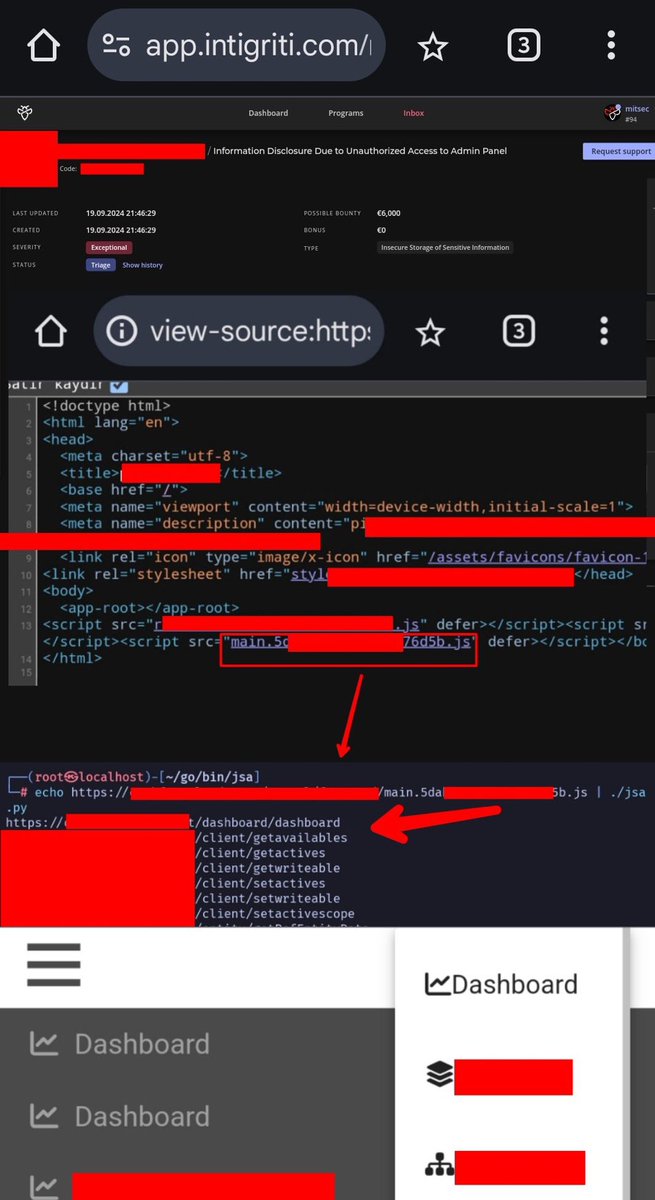
always examine the .js files in the source code, for this I can recommend this simple but effective tool github.com/w9w/JSA from here you can access the endpoints of critical data, the places where backup files are stored and many endpoints credit: Yunus Emre Öztaş #BugBounty















"MCP is a client-server architecture whereby the AI application acts as a client and MCP servers deliver external service data back to the application." Read more: blackhillsinfosec.com/model-context-… Model Context Protocol (MCP) by: ʝօʄʄ ȶɦʏɛʀ 🇦🇺🇺🇸 @yoda66.bsky.social Published 10/22/2025