
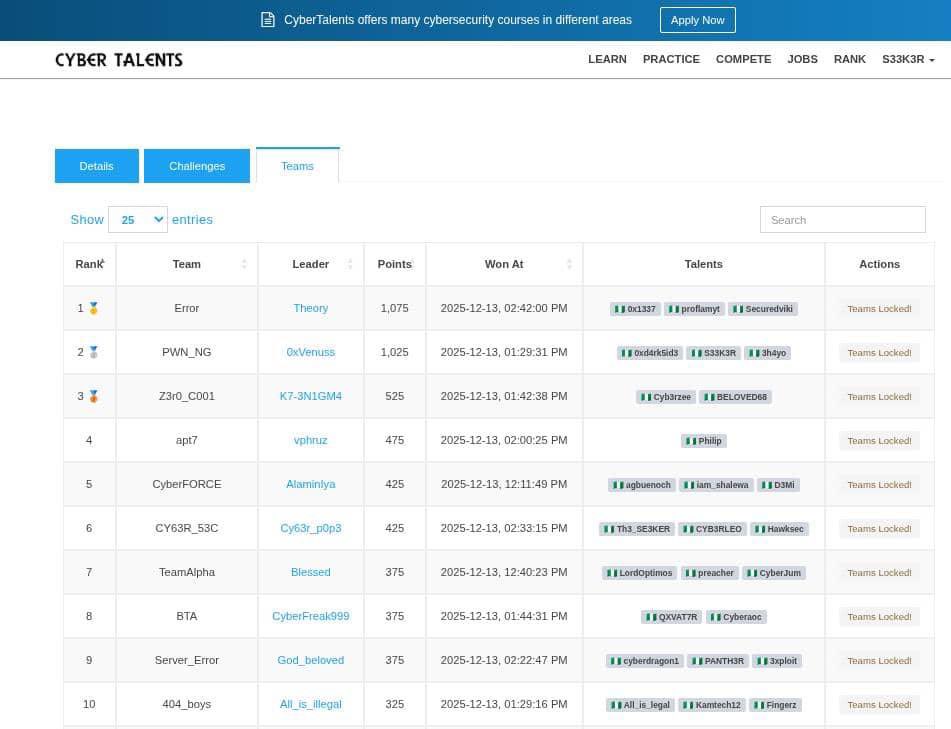
sh4yo
@3h4yo
Student || CTF Player || Pentester/ Red Teamer || n00b || still learning..........
ID: 1499301478166667265
https://github.com/shayol33 03-03-2022 08:31:56
668 Tweet
495 Takipçi
1,1K Takip Edilen



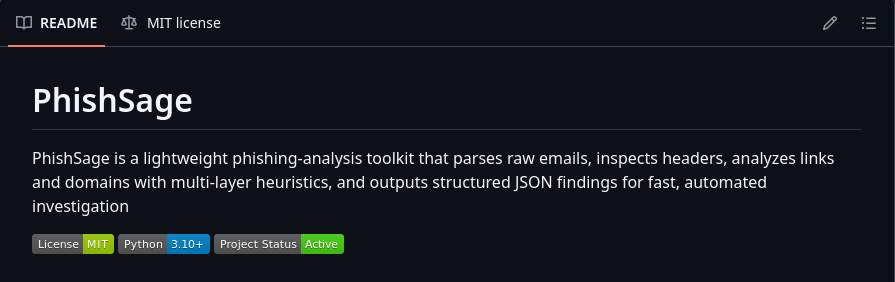
🛡️ PhishSage: A lightweight email security toolkit for analyzing headers, attachments, and links. Offers quick insights, heuristics, and enrichment in JSON or readable summaries. 🔗 GitHub: github.com/0xlam/PhishSage Dr Iretioluwa Akerele #Phishing #Infosec #Cybersecurity #Security #OpenSource








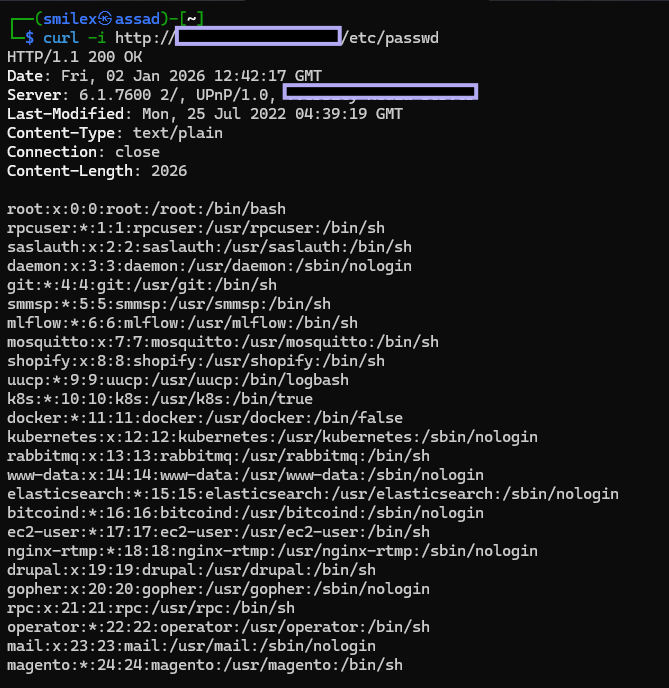
Shodan+Nuclei (Nuclei by ProjectDiscovery ) = Bounties 💸, Tip:Got LFI? Don't stop at /etc/passwd. Try reading private SSH keys (~/.ssh/id_rsa) to get a direct shell. 🐚 #BugBounty #bugbountytips #TrendingNow #RCE #NucleiTemplates #CyberSec

Completed the Active Directory Attack Path in Action webcast by Black Hills Information Security A practical look at how attackers chain small weaknesses to escalate from uncredentialed access to Domain Admin. Always learning. Always improving. #ActiveDirectory #BlackHillsInfosec






![Black Hills Information Security (@bhinfosecurity) on Twitter photo "[...] Kerberos delegation is easily among my top favorite vectors of abuse, and [...] I’ve noticed that Impacket doesn’t get nearly as much coverage as tools like Rubeus or Mimikatz.
Read more: blackhillsinfosec.com/abusing-delega…
Abusing Delegation with Impacket (Part 1): Unconstrained "[...] Kerberos delegation is easily among my top favorite vectors of abuse, and [...] I’ve noticed that Impacket doesn’t get nearly as much coverage as tools like Rubeus or Mimikatz.
Read more: blackhillsinfosec.com/abusing-delega…
Abusing Delegation with Impacket (Part 1): Unconstrained](https://pbs.twimg.com/media/G-0DwcaWwAEiGpq.jpg)


