Is your organization taking a 'threat-informed' approach to cybersecurity? Watch the video to see how Palo Alto Networks Unit 42 is helping organizations identify and contain the #Log4j vulnerability. #SecuredByPANW stuf.in/bdsigb



1/ Context: Much debate in policy circles & industry about need to fund OSS to support #digitalsovereignty , national competitiveness in science/technology & #softwaresecurity (esp. after vulnerabilites like #log4j )
Great blog on this by Matthew Hodgson: matrix.org/blog/2024/04/o…


Log4Shell is the attack that made us aware of the security risks if we are not careful in network programming in Java. With this book, you will know what to watch out for.
#javaprogramming
#Security
#vulnerability
#Programmer
#Log4Shell
#AWS
amazon.com/dp/B09PH9WZRP/…
6KRC7JYv

Richi Jennings @[email protected] / @richi.bsky.social Techstrong Group Security Boulevard Looooool You'll still believe the story of the trainee who left a hardcode password ... when everything links the attack to #log4j #javapocalypse

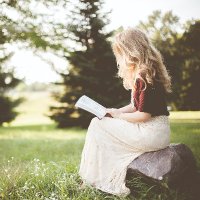
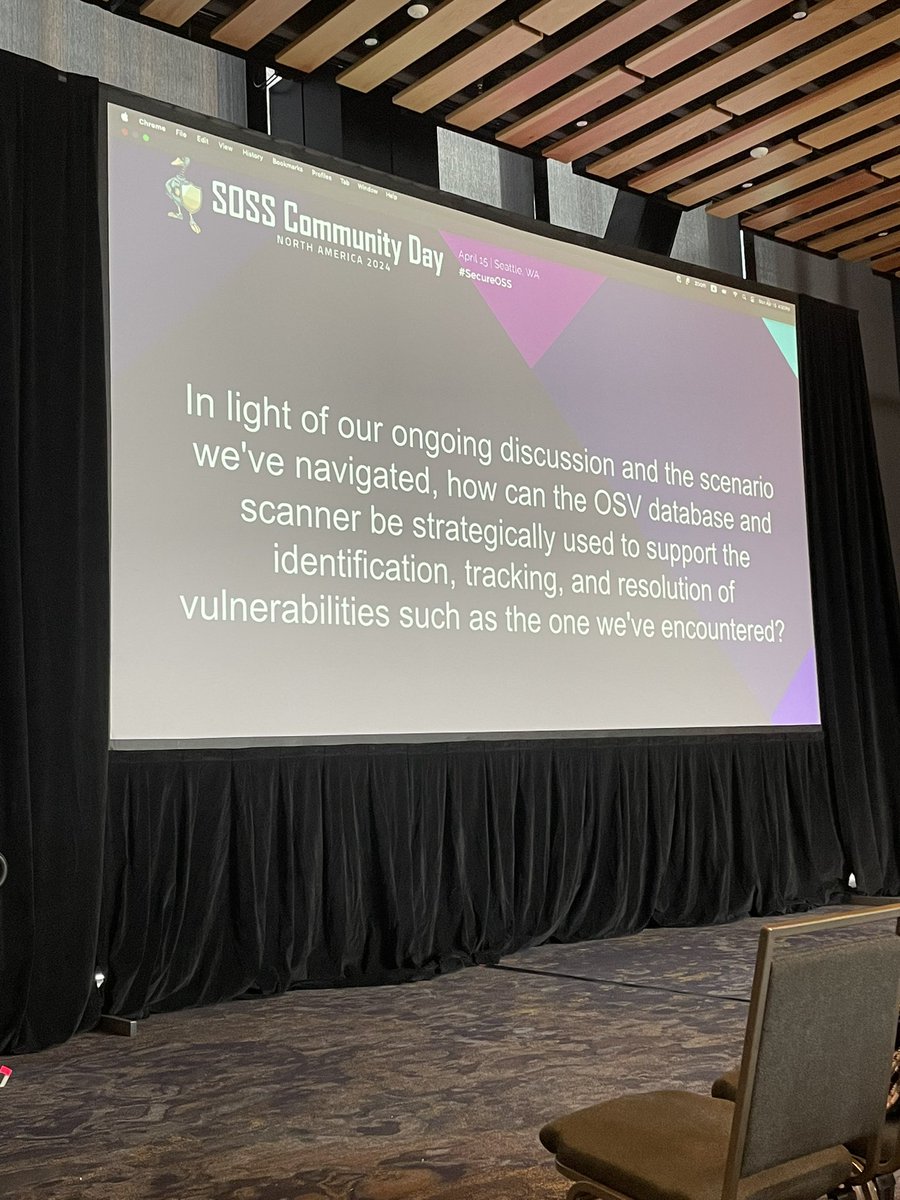
OSV database — aims to be precise about versions affected, recommendations about whether you’re vulnerable, and allow for automations.
For example, log4j is 6 levels deep, and all 6 levels need to be patched. Versus something surface level
Prioritize by impact.
#SOSSCommunity

tatematsu_san 近年スコア10で対応が重かったのは Log4j があったなぁと思いつつ、あれからもう 2年半経過しているのか...
それなのに Log4j 対応のパッチすらあててない環境をよく目にするんですよね...なんと言うか BCP としてセキュリティやパッチ適用って概念が欠落しているケースが多い


Sherrod DeGrippo 🦓 SwiftOnSecurity Never mind the fact that the quote tweet is just plain incorrect. Java has the same kind of ecosystem of libraries. The now infamous Log4j is a common Java library.

Lisa Forte Qualys One question. On Azure does the Qualys environment scan static images on the backplane or storage that arent started? During Log4J we had to do that on AWS in a hurry and given what is going on tonight with … every … single … firewall … vendor… i can see it being needed